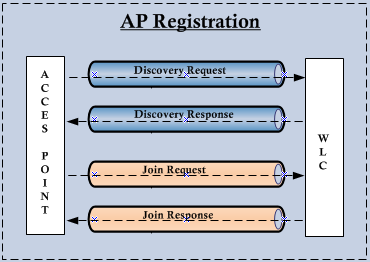
AP Registration to a WLC is two parts; the discovery & the join phase. Following diagram shows this concept.
Usually Discovery request handled by Management Interface of a WLC & Join Requests handled by AP-Manager Interface. In 5508 only management interface available & it act as AP-Manager interface for these join request.
These are the steps AP will go through in order to register with a WLC.
Step 1. AP begins with a WLC discovery & join phase. AP send CAPWAP discovery request messages to WLC.
Step 2. Any WLC receiving the CAPWAP discovery request responds with an CAPWAP discovery response message.
Step 3. From the CAPWAP responses received from WLCs, AP selects a WLC to join.
Step 4. AP sends a CAPWAP join request to the WLC, expecting CAPWAP join response.
Step 5. WLC validates the AP and then CAPWAP join response to the AP. The AP validates the WLC to complete the discovery & join process. The validation on both the AP & WLC is a mutual authentication mechanism.An encryption key derivation process occur subsequently and that ensure future CAPWAP control messages are encrypted.
First challenge is to find where to send CAPWAP discovery messages ? AP first go through a hunt process to find a WLC. Here are the different methods AP can used for this. The order of these are not important
1. AP issues a DHCP discover request to get an IP address, unless it has previously configured static IP.
2. AP send a layer 3 local broadcast(255.255.255.255) message to find a WLC
3. DHCP Option 43 in the DHCP offer messages.
4. DNS- AP try to resolve CISCO-CAPWAP-CONTROLLER.local-domain or CISCO-LWAPP-CONTROLLER.local-domain to find an IP of a WLC
5. Previously known WLC IP, AP will rememberup to 24 previosly learnt WLC IP address & send discovery to them.
6. Statically configured from WLC
7. Statically Configured from AP CLI
To see AP registration process in detail will remove CAPWAP AP configurations in order to remove the previously known IP. You can do this as follows via AP CLI.
LWAP-02#debug capwap console cli This command is meant only for debugging/troubleshooting Any configuration change may result in different behavior from centralized configuration. CAPWAP console CLI allow/disallow debugging is on LWAP-02#erase /all nvram: Erasing the nvram filesystem will remove all files! Continue? [confirm] [OK] Erase of nvram: complete LWAP-02#reload Proceed with reload? [confirm] Writing out the event log to nvram..
Once rebooted it will complain about no IP. Yes without IP AP cannot do anything to register with WLC.
AP5475.d0dd.a488> *Mar 1 00:00:32.955: %LINK-3-UPDOWN: Interface Dot11Radio1, changed state to up *Mar 1 00:00:32.983: %LINK-3-UPDOWN: Interface Dot11Radio0, changed state to up *Mar 1 00:00:33.935: %LINEPROTO-5-UPDOWN: Line protocol on Interface Dot11Radio1, changed state to up *Mar 1 00:00:33.935: %SYS-6-LOGGINGHOST_STARTSTOP: Logging to host 255.255.255.255 started - CLI initiated *Mar 1 00:00:33.963: %LINEPROTO-5-UPDOWN: Line protocol on Interface Dot11Radio0, changed state to up *Mar 1 00:00:38.719: %CAPWAP-3-ERRORLOG: Not sending discovery request AP does not have an Ip !! *Mar 1 00:00:48.719: %CAPWAP-3-ERRORLOG: Not sending discovery request AP does not have an Ip !!
Let’s configure static IP & see the console output( Remember that I have not configure the switch port for any access vlan yet). Since these are lightweight image we cannot configure like normal IOS AP. So here are the command to do this.
capwap ap ip address 10.10.113.5 255.255.255.0 capwap ap ip default-gateway 10.10.113.1 capwap ap controller ip address 10.10.111.10
Since I have not configured the switch port for vlan 113, still AP cannot reach its gateway. Then AP try to reboot & see to learn an IP again.
AP5475.d0dd.a488#
*Mar 1 00:11:09.499: %CAPWAP-3-STATIC_TO_DHCP_IP: Could not discover WLC using static IP. Forcing AP to use DHCP.
Now we will configure our switch port (fa1/0/12) to access vlan 113. This time you can see AP successfully able to complete Discovery & Join process as it can reach WLC. Note that since I have 4402 WLC it has AP manager interface with an IP (10.10.111.11) which respond to Join Request. (see below)
Press RETURN to get started! Translating "CISCO-CAPWAP-CONTROLLER"...domain server (255.255.255.255) *Mar 1 00:00:31.107: %CAPWAP-5-CHANGED: CAPWAP changed state to DISCOVERY *Mar 1 00:00:32.923: status of voice_diag_test from WLC is false *Mar 1 00:00:32.951: %SSH-5-ENABLED: SSH 2.0 has been enabled *Mar 1 00:00:32.971: Logging LWAPP message to 255.255.255.255. *Mar 1 00:00:34.747: %CDP_PD-4-POWER_OK: 15.4 W power - NEGOTIATED inline power source *Mar 1 00:00:34.775: %LINK-3-UPDOWN: Interface Dot11Radio1, changed state to up *Mar 1 00:00:34.803: %LINK-3-UPDOWN: Interface Dot11Radio0, changed state to up *Mar 1 00:00:35.755: %LINEPROTO-5-UPDOWN: Line protocol on Interface Dot11Radio1, changed state to up *Mar 1 00:00:35.755: %SYS-6-LOGGINGHOST_STARTSTOP: Logging to host 255.255.255.255 started - CLI initiated *Mar 1 00:00:35.783: %LINEPROTO-5-UPDOWN: Line protocol on Interface Dot11Radio0, changed state to up Translating "CISCO-LWAPP-CONTROLLER"...domain server (255.255.255.255) Translating "CISCO-CAPWAP-CONTROLLER"...domain server (255.255.255.255) *Mar 17 08:50:18.000: %CAPWAP-5-DTLSREQSEND: DTLS connection request sent peer_ip: 10.10.111.11 peer_port: 5246 *Mar 17 08:50:18.000: %CAPWAP-5-CHANGED: CAPWAP changed state to *Mar 17 08:50:18.567: %CAPWAP-5-DTLSREQSUCC: DTLS connection created sucessfully peer_ip: 10.10.111.11 peer_port: 5246 *Mar 17 08:50:18.567: %CAPWAP-5-SENDJOIN: sending Join Request to 10.10.111.11 *Mar 17 08:50:18.567: %CAPWAP-5-CHANGED: CAPWAP changed state to JOIN *Mar 17 08:50:18.707: %CAPWAP-5-CHANGED: CAPWAP changed state to CFG *Mar 17 08:50:18.835: %LWAPP-3-CLIENTERRORLOG: Operator changed mode for 802.11g. Rebooting. *Mar 17 08:50:18.887: %LINK-5-CHANGED: Interface Dot11Radio0, changed state to administratively down *Mar 17 08:50:18.895: %SYS-5-RELOAD: Reload requested by CAPWAP CLIENT. Reload Reason: Operator changed mode for 802.11g. *Mar 17 08:50:19.887: %LINEPROTO-5-UPDOWN: Line protocol on Interface Dot11Radio0, changed state to down IOS Bootloader - Starting system.
If you took a wireshark packet capture of the WLC connected switch port you can see the details of each of these types of packet. See below wireshark capture shows different type of packets in discovery process.
Here is the Discovery Request packets details. Note that discovery request is sent to WLC management IP with destination port UDP 5246 (capwap-control). Also Message Element value 1 which indicate Static Configuration. Different IE value indicates the type of discovery method used. We will see few other options (DHCP, DNS, Broadcast) discovery in some other post.
0- Broadcast
1- Configured
2- OTAP
3- DHCP Server
4- DNS
Here is the discovery response packet. As you can see WLC is providing all the information to AP (including WLC IP – AP mgr, Name, etc)
Then AP send the Join Request & expecting Join Response from WLC. First step is to establishing a secure CAPWAP connection with complete DTLS handshake as shown in the packet capture. This include Client Hello, HelloVerifyRequest/ ClientHello(with Cookie), ServerHello/Certificate, ClientKeyExchange/ ChangeCipherSpec, ServerChangeCipherSpec (See below)
Subsequent traffic is DTLS encrypted & cannot be decode to see what’s inside. You can disable encryption for CAPWAP by using “test capwap encr <ap-name> disabe” command on WLC CLI or “test capwap dtls ctrl disable” on AP CLI.
AP5475.d0dd.a488#test capwap dtls ctrl disable
*Mar 17 09:54:15.891: Capwap Control packets will not be encrypted
But once I disable it , AP could not join the WLC & could not verify the complete process without DTLS encryption. In HREAP mode you can do this & see this complete process without encryption( Refer How Does OEAP Works for more detail).
Related Posts
1. Split MAC vs Local MAC Architecture
2. WLC Discovery via DHCP Option 43
3. WLC Discovery via DNS
4. WLC Discovery via Broadcast
5.




A million Thanks to you for this blog.
Thanks Ashish….
While the order is not important for real life they ask about it in the CCIE written exam
True 🙂
Hi Nayarasi, my name is Denny. Can you help me to configure my Aironet 2600 series, it’s won’t discover on my WLC, thanks and I appriceate for you help 🙂
Hey Rasika,
I am trying to migrate APs (2702i) from WLC 2500 on 8.0.100 to a new WLC 8510 on 8.0.110. These APs were working fine and they were configured as flexconnect modes. It looks like my APs are stuck somewhere in between the migration process. I can see the discovery request and respose from these APs to the new controller. But I dont see any join request coming to the WLC. The APs are remote so i can not console into them for now. Doing “debug capwap events enable” gives me this line of output…
“*spamApTask2: Jul 07 10:21:59.438: [PA] acDtlsPlumbControlPlaneKeys: lrad:10.243.148.32(14482) mwar:172.17.101.105(5246)”
For migration, i already have the DNS entry pointing to the new controller and I have configured the new controller IP on the high availability tab of each AP.
any help is apprecaited. Thanks!
More info on this….
(Cisco Controller) >show ap join stats detailed f4:4e:05:dc:52:d0
Sync phase statistics
– Time at sync request received………………………. Not applicable
– Time at sync completed…………………………….. Not applicable
Discovery phase statistics
– Discovery requests received………………………… 147
– Successful discovery responses sent…………………. 147
– Unsuccessful discovery request processing……………. 0
– Reason for last unsuccessful discovery attempt……….. Not applicable
– Time at last successful discovery attempt……………. Jul 08 08:26:43.525
– Time at last unsuccessful discovery attempt………….. Not applicable
Join phase statistics
– Join requests received…………………………….. 0
– Successful join responses sent……………………… 0
– Unsuccessful join request processing………………… 0
– Reason for last unsuccessful join attempt……………. Not applicable
– Time at last successful join attempt………………… Not applicable
– Time at last unsuccessful join attempt………………. Not applicable
Configuration phase statistics
–More– or (q)uit
– Configuration requests received…………………….. 0
– Successful configuration responses sent……………… 0
– Unsuccessful configuration request processing………… 0
– Reason for last unsuccessful configuration attempt……. Not applicable
– Time at last successful configuration attempt………… Not applicable
– Time at last unsuccessful configuration attempt………. Not applicable
Last AP message decryption failure details
– Reason for last message decryption failure…………… Not applicable
Last AP disconnect details
– Reason for last AP connection failure……………….. Not applicable
– Last AP disconnect reason………………………….. Not applicable
Last join error summary
– Type of error that occurred last……………………. None
– Reason for error that occurred last…………………. Not applicable
– Time at which the last join error occurred…………… Not applicable
AP disconnect details
– Reason for last AP connection failure……………….. Not applicable
It looks like my APs are affected by this bug.
http://serialnumbervalidation.com/63916/cgi-bin/index.cgi
Everything is working fine for me now. Thanks.
Your are awesome, thanks for your help
Thanks
Hi, We are trying to register 3700 AP to 5520 WLC with 8.1.102 code running and we are seeing LCB allocation failed for the new AP under ap join response section error in AP join status on controller. Any idea what is this issue ? Controller time base is correct and sync. There are two firewalls in between AP subnet and WLC. we have opened udp/5246-5247 and udp/12222 and udp/12223 ports bi-directional but still APs are not joining
Hi Nithin!
Were you able to fix it? I got the same issue.
Stefan
Hi yes I was able to fix it up. It was firewall rule issues we had to correct firewall rules in order to allow controller to send response to ap subnet.
The error “LCB allocation failed for the new AP” was also experienced under WLC version 8.2 when attempting to join APs under the 12-week evaluation license, but not having accepted the EULA:
(Cisco Controller) >show license summary
Feature name: ap_count
License type: Evaluation
License Eula: Not Accepted
Evaluation total period: 12 weeks 6 days
License state: Active, Not-In-Use
RTU License Count: 1500
(Cisco Controller) >license activate ap-count eval
…… follow prompts to accept the EULA…….
(Cisco Controller) >show license summary
Feature name: ap_count
License type: Evaluation
License Eula: Accepted
Evaluation total period: 12 weeks 6 days
License state: Active, In-use
RTU License Count: 1500
And then the APs completed the join process.
For 2 days, I have been struggling to bring up a 2504 controller and cap3602I. Both of which had old software versions going back 2013. I was able to upgrade the controller from 7.6 to 8.0.121 without any issues. After entering the static IP, bam, my 3602I AP joined the WLC and upgraded itself. Thank you.
Great, make sure you configure WLC name & IP address in AP High Availability ( primary, secondary, )tab once registered the AP to WLC
Hi Guys,
Is it possible to assign Static IP address to Cisco 1832/1852 AP? If so, what are the CLI commands? I can only see the capwap ap primary-base . Thanks in advance!
i am facing problem in joining 1552e AP with 5508 WLC
Layer 3 discovery request not received on management VLAN
Pls open a thread in CSC forum given below. You will get faster response to troubleshoot your issue.
https://supportforums.cisco.com/community/5956/getting-started-wireless
HTH
Rasika
Need to add their the mac to the MAC filter. I have 2 have them and had the same issue. it is under security tab
Thanks Greg
Hi Nayarasi,
we have cisco 5508 wlc and 180 numbers of 702i APs installed at multiple locations.
its been a three months for the setup, earlier all were working fine but recently we are getting problems at some locations. i.e.
AP shows TRANSLATING CISCO CAPWAP …….Controller (255.255.255.255) error
and LED starts blinking RED,GREEN,BLUE,ORANGE, the error remains same untill and unless we RESET the AP after working fine for sometimes it again shows the same error.
kindly help me in this………
plz do revert to me for more clarifications.
Thanks.
Hi Sajid,
It seems due to some reason those AP lost its controller & cannot find it again for registration. Could be a bug of the software code/AP model.
Have you reach Cisco TAC on this ?
HTH
Rasika
Hi,
Any thoughts on how to decommission a Cisco wireless controller remotely ?
If you simply want to factory default WLC configuration, you can reload this current WLC & “Recover-config” on CLI. Refer below
https://supportforums.cisco.com/document/8941/how-reset-wireless-lan-controller-wlc-factory-defaults
HTH
Rasika
Hi,
I am using 8510 WLC and cisco 2700, 3700 access point. currently, I am facing an issue of few access points are disconnecting with short period of time. I did PoE off and then on from the connecting switch port. so after that, they all are connect successfully for a short period of time and again disconnected from the WLC. how to solve this issue.?
seems like software defects
Im looking to write a procedure on adding a new AP to a WLC.
Does anyone have a good step by step process I can start with.
Something mid-level and I can expand on from plugging AP into the switch and configuring port to renaming new AP in WLC.
Thanks,
Gene
Hi,
from my point of view, start with considering how the AP obtains WLC IP address (local bcast, DNS, DHCP, manual priming), Define these steps (DHCP Option 43 documentation from Cisco, DNS configuration, CLI commands to manual prime AP). Document WLC IP Address and Firewall rules included for AP to reach WLC using CAPWAP ports. Document necessary switch-port config (either local-mode or Flexconnect, consider VLANs and possibly 802.1x/ port-security (is this still a thing?) on the switchport. Also consider PoE and requirements (802.3af/at). Upon connecting the AP to the network, take a debug from WLC and AP on successful join and highlight critical steps. After that, Using Either WLC GUI or CLI (whichever suits you better) rename AP, assing mode, assign AP group, consider Flexconnect, Ensure AP admin mode and radios are set to enabled state.
Once done, document AP radio settings, channel and power-level, check (for FC) if VLAN assignments were required and are working.
I have no solid documentation on this by my own right now but I think this is a good startingpoint.
Hi ,
I have 3 Controller in Setup and I need only one to be use for registration purpose .
How is it possible that the request from new AP goes to only 1 WLC or only that WLC respond back .
I need like disable the request response on WLC that are not used as registration purpose.
Hi
I am using controller 2500. I am trying to integrate stand alone AP which has been converted into Controller based AP. but it showing last logs as Nov 24 14:03:25.343: %CAPWAP-5-SENDJOIN: sending Join Request to
it’s not joining to the controller can you help in this?
What AP model you got and what software version running on your WLC ?
Refer below guides
1. http://www.cisco.com/c/en/us/td/docs/wireless/compatibility/matrix/compatibility-matrix.html
2.
http://www.cisco.com/c/en/us/support/docs/wireless/5500-series-wireless-controllers/119286-lap-notjoin-wlc-tshoot.html
HTH
Rasika
I usually go through your web for wireless help, I found your web very useful. I am stuck with Cisco 3605 AP for a registration with the Cisco virtual WLC. The AP is keeping trying to resolving CICSO-LWAPP-CONTROLLER. The environment is running a dhcp where I neither I can configure option 43 nor host entry for CICSO-LWAPP-CONTROLLER in the DHCP server.
The AP console is not allowing me to enter anything in the console, it is keep renewing the IP address from the DHCP to get the controller IP address in the either by option 43 or by resolving the name.
Please give me help on this.
Try to put AP on to the same as WLC management interface vlan & see
HTH
Rasika
Hi
Both the AP and vWLC are in same subnet, but AP still tyring to discover the controller. The AP is not allowing me to enter any command in the console. The AP is keep showing messages of DCHP renewing address and search controller.
How can I enter the command in AP console?
#debug capwap console cli
Enter the above command & then you should be able to issue those CLI commands.
Rasika
FYI on capwap control packet encryption, test capwap encr was removed from 8.0 code per CSCut91240.
Thanks for detail.
It seems Cisco does not want this command to be available any further
HTH
Rasika
Great explanation !
Thanks Mahesh
Hi Nayarasi,
I´m Luciano from Brazil, and I have a Serie 1600 and my AP give this message after update Firmware to version Most actual.
Not in Bound state.
*Mar 1 00:14:51.471: %CAPWAP-3-DHCP_RENEW: Could not discover WLC. Either IP address is not assigned or assigned IP is wrong. Renewing DHCP IP.
*Mar 1 00:14:54.546: %DHCP-6-ADDRESS_ASSIGN: Interface BVI1 assigned DHCP address 192.168.11.27, mask 255.255.255.0, hostname APf40f.1bc4.700d
Translating “CISCO-CAPWAP-CONTROLLER.revicom.local”…domain server (192.168.11.1)
What can I do to solve this, can you help me please.
Thank you so much in advanced.
regards,
Luciano.
Do you have a WLC ? Looks like you have upload a lightweight image that require a WLC
Rasika
Hi Rasika,
No I dont have WLC (Wireles Lan Controler), this equipament is only for uses in AP WIFI, maybe I updated with wrong IOS???
I want uses this equipament only for WIFI.
Do you have any suggestion, whata can I do??
Look Description of my AP
Cisco IOS Software, C1600 Software (AP1G2-K9W8-M), Version 15.3(3)JF, RELEASE SOFTWARE (fc4)
Technical Support: http://www.cisco.com/techsupport
Copyright (c) 1986-2017 by Cisco Systems, Inc.
Compiled Tue 25-Jul-17 01:08 by prod_rel_team
ROM: Bootstrap program is C1600 boot loader
BOOTLDR: C1600 Boot Loader (AP1G2-BOOT-M) LoaderVersion 15.2(2)JAX, RELEASE SOFTWARE (fc1)
APf40f.1bc4.700d uptime is 4 minutes
System returned to ROM by power-on
System image file is “flash:/ap1g2-k9w8-mx.153-3.JF/ap1g2-k9w8-xx.153-3.JF” – This is the version of I Update.
Last reload reason:
cisco AIR-CAP1602E-T-K9 (PowerPC) processor (revision B0) with 187386K/74672K bytes of memory.
Processor board ID TSP1838AAHP
PowerPC CPU at 533Mhz, revision number 0x2151
Last reset from power-on
LWAPP image version 8.5.103.0
1 Gigabit Ethernet interface
2 802.11 Radios
32K bytes of flash-simulated non-volatile configuration memory.
Base ethernet MAC Address: F4:0F:1B:C4:70:0D
Part Number : 73-14508-04
PCB Serial Number : TSP18373374
Top Assembly Part Number : 800-38553-03
Top Assembly Serial Number : TSP1838AAHP
Top Revision Number : A0
Product/Model Number : AIR-SAP1602E-T-K9
Thank you so much Rasika.
Regards,
Luciano.
Yes, you have uploaded the wrong image. Look for k9w7 for autonomous ap
Regards
Rasika
Thank u very much for your great support
No worries Kennedy, glad to see it is useful to you
Rasika
Good day and THANK YOU for all of your awesome posts! I find them all very enlightening. I am currently upgrading / migrating from three 5508 controllers to two 5520 controllers. I find it interesting the minimal downtime the AP (and associated clients) see when I change the Primary Controller (in HA tab of AP) as this is how I’m moving them from the old WLC to the new WLC. I would suspect that the CAPWAP tunnel to the old WLC stays up and functional until the new CAPWAP tunnel is built and ready to pass traffic to the 5520 WLC. I think I need to watch debug for the AP MAC address on old and new WLC simultaneously to verify this, but it is a REALLY quick process / minimal outage to the client when they migrate over to new WLC. I’d love to hear your experience and/or input on the subject. Thanks again for your tremendously useful posts! Cheers…
Hi Jeff,
Thanks for kind remarks.
I assume your 5520 & 5508 got same image versions. Also do you have mobility peering with 5520 & 5508 ? I have upcoming work involve similar migration, will let you know once I have tested in that environment.
Yes, if you could have some packet capture (AP connected switchport), that would be really helpful to see the clear steps with timing involve.
Rasika
What are the reasons why the AP tears down its CAPWAP tunnel to the controller?
I have two controllers on my test environment (same subnet), no WLC in master controller mode, the AP is not configured with primary, secondary and tertiary WLC. Upon checking, AP is joined first with WLC1 but then switch to and joined WLC2, AP does not reboot nor encountered power loss, same uptime. I am wondering what is the possible reason for this? Any thoughts?
Thank you! 🙂
Hi Rasika,
Thank you for this great guide.
I have 15 APs (2700, 2800, 4800 series) that are registered to the local physical WLC (55xx series) and I need to move them to the new, virtual WLC (9800).
IPs have dynamically assigned IP parameters from DHCP server, including option 43 with the IP address of the physical WLC.
What is the best way to move those APs to the vWLC with minimal AP downtime?
I saw there is option to go to the physical controller, navigate to AP, and from there manually set IP address of the controller (in this case I would use vWCL’s IP) and reload AP. Do you think this will work, did you have any similar experience?
Hi Mark, My advice is first get 9800 controller configured properly. You can use below tool to help with that
https://community.cisco.com/t5/other-wireless-mobility-subjects/wlc-config-converter-aireos-ios-xe/td-p/2895495
Since configuration options changed in 9800, first familiarize with it. Then I would suggest you to test new config with one AP (test AP or take one out of production). Your WLAN client should get authenticated/recv IP/etc.
Once you comfortable with new 9800 setup, then you can go ahead and change primary controller IP/name (under individual AP High Availability tab), so all of those AP registered to new 9800 & things should work, as you have verified earlier.
HTH
Rasika
Hi Rasika,
I didn’t know this tool exists, I will save it for the future, it seems to be very useful 🙂
Back to my question, my 9800 controller is already setup and 2 recently built offices with 9130AX APs are already running with it, so the configuration of the 9800 is ready.
What I need now is to move APs in the old office from local physical controller Cisco 2500 to the new 9800 controller in the DC.
So, do you think that this approach with editing primary controller IP/name (under HA tab) and reloading AP might work in this case?
Thank you for the help!
Hi Tokwa,
Did you configure the High Availabilty on the AP,like which is primary and which is secondary WLC.If you have configured , Try to make the priority as High , If still you are facing the issue take the debug on the both the WLC for that AP and analyze the debug logs.
And Lastly try to Factory reset the Access point and configure newly and check.
Hi Rasika, sir,
this is awsome daignose steps you shared me to clear my issues, Thanks a lot
Thank you Avinash