It is hard to believe that another year has flown by, but the Wi-Fi Knowledge Summit (Wi-Fi KS) 2026 in Bangalore, India, has just wrapped up! Organized by Nanoeell Networks under the leadership of my close friend Dr. Srikanth, this annual two-day event continues to be the premier gathering for wireless practitioners, network engineers, and vendors in the region.
This was my second year traveling from Australia to attend the summit in person at the Radisson Blu Atria. While you can watch technical presentations on YouTube, nothing replaces the value of face-to-face human interaction, building international friendships, and motivating the next generation of engineers.
If you couldn’t make it to Bengaluru this year, here is a complete recap of what went down across the pre-conference training and the main summit event.
Day 1: Pre-Conference Training (Wi-Fi 7 in Action and a Sneak Peek at Wi-Fi 8)
The summit kicked off with a dedicated day of deep-dive technical workshops. I had the privilege of delivering a session focused on WPA3 and OWE deployment strategies in the Wi-Fi 7 era.
With the shift toward 6 GHz and the mandatory requirement for protected management frames, understanding the real-world behavior of security transitions is critical. Thanks to the team at Candela Technologies, we were able to run live packet captures during the class to analyze exactly how client devices negotiate WPA3 and OWE. The audience interaction was fantastic, with excellent questions surrounding enterprise deployment challenges.

Day 2: The Main Summit & Presentation Highlights
The main conference brought together a brilliant lineup of speakers covering everything from the latest Wi-Fi 7 hardware capabilities, experimental results, to advanced protocol analysis. & telemetry. You can watch these recorded session once it is published on the Wi-Fi KS page.
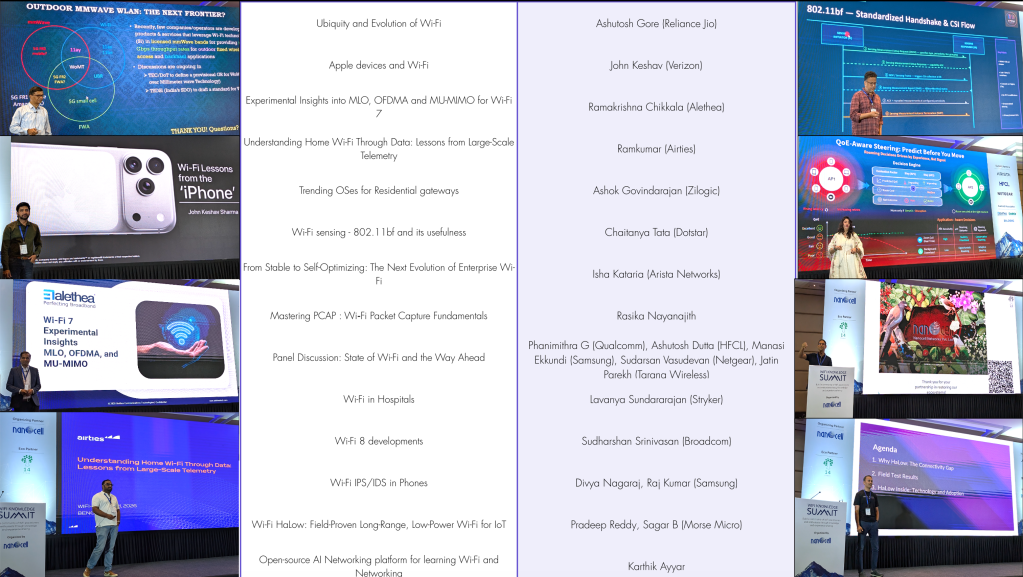
During the general sessions, I presented on a topic close to my heart: “Mastering Wi-Fi PCAP Analysis“. My session focused on the various methods engineers can use to capture clean packets over the air and how to effectively analyze them using free, open-source tools.

The Real Value: Community, Inspiration, and Giving Back
More than just the slide decks, this conference is about the people. I had the pleasure of catching up with wireless veterans like Senthil (CWNE #15), a longtime industry veteran.

But one of the most rewarding moments of the entire trip happened when I met Sandeep from Cisco. He came up to tell me that he had been following my blog and my wireless journey for a long time, and that it inspired him to push through his studies to recently achieve his CCIE Wireless status! Hearing stories like that is exactly why I continue to create content and travel for these events—mentorship and paying it forward are what keep our industry vibrant.

I had a good interaction with both Alethea and Candela Technologies, where they showcased their latest testing products.

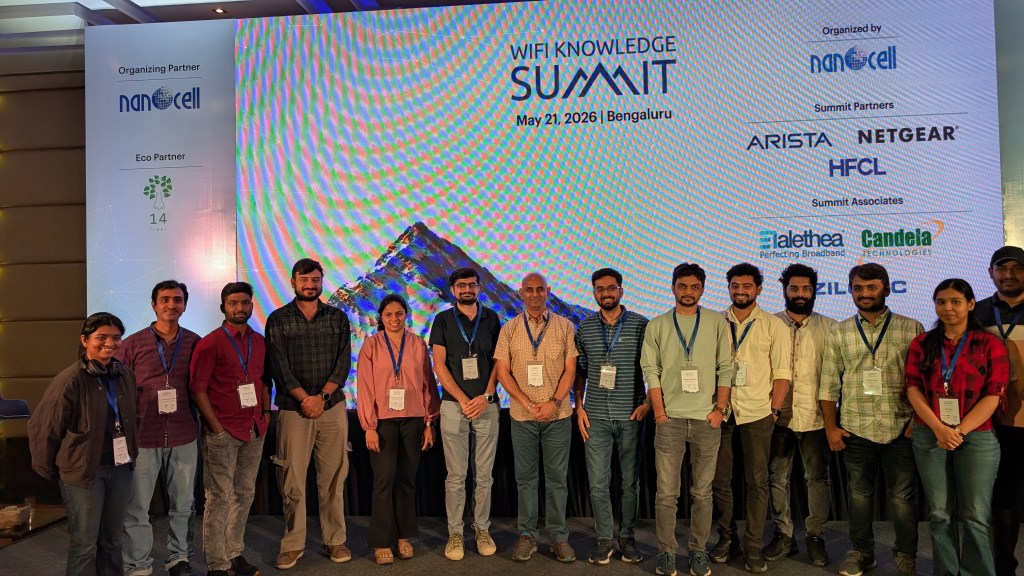
I always enjoy conversations with Sitarama, who brings a lot of positive energy to the table. His team did an excellent job supporting both days and covering the event’s social media promotion.


Arista, HFCL, and Netgear were the summit partners this year. Here are some of them who took the opportunity to take photos with Srikanth and Devdas from Nanocell.

I took an extra day this year as well to spend time with the Alethea and Candela teams (last year I visited the Cisco office, and you can read more about it in this post). First, we visited the Alethea office and had a good conversation with them about the challenges they are facing with certain enterprise Wi‑Fi AP testing. We had lunch with them afterward, and here is a photo with Rama and Neil from Alethea.

Then I visited the Candela office at Acharya Institute of Technology in Bangalore. Although it is a bit far from the main city, I liked the college environment where they tap into fresh graduates and provide mentoring and career guidance in the wireless testing industry. I can see Candela’s young engineers performing really well in presenting and knowledge sharing within the Wi‑Fi community. I encourage them to pay it forward as they grow.

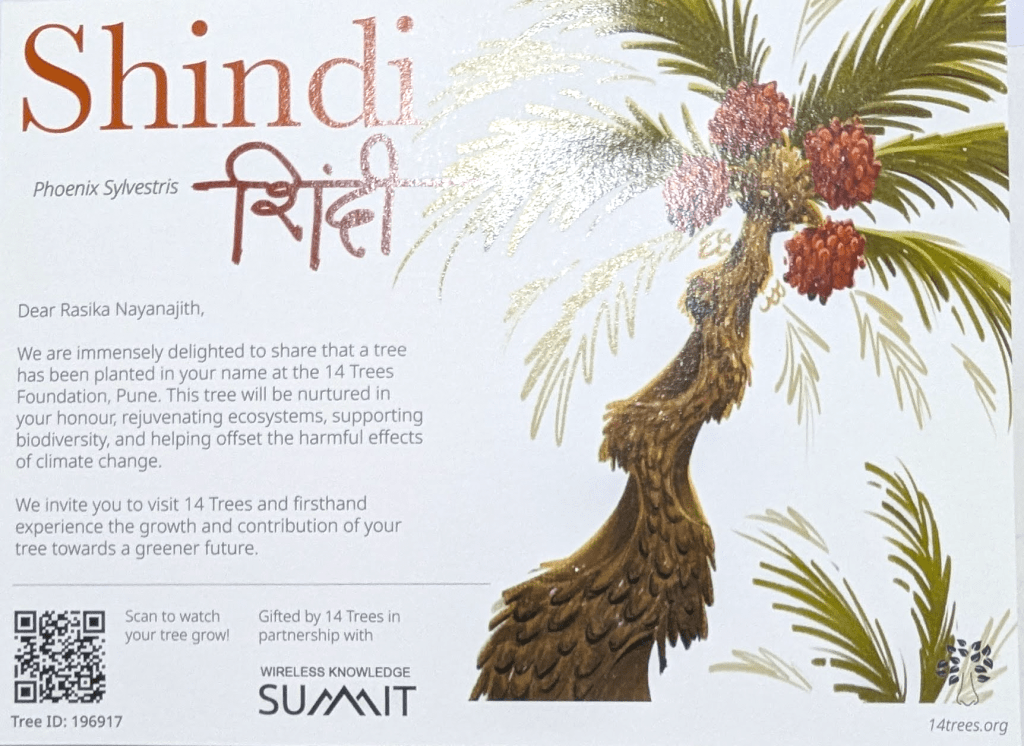
On a final note, I love the commitment to sustainability that Nanocell has integrated into the summit. In honor of the environment, the co-founders have a green initiative (14trees.org) where a tree is planted on behalf of every speaker at the event. I look forward to visiting the tree planted in my name on one of my future trips to India! Here is the tree detail planted in my name.
Looking forward to be at Wi-Fi Knowledge Summit 2027
