EAP-FAST (Flexible Authentication via Secure Tunneling) initially developed by Cisco. Later in 2007, IETF ratified this in RFC 4851. Cisco developed this as replacement for LEAP. EAP-FAST provide both mutual authentication & tunnelled authentication without using standard based X.509 digital certificate to create TLS tunnels, instead use PACs (Protected Access Credentials)
A PAC can consist of 3 components
1. Shared Secret – PAC key
2. Opaque Element – PAC-Opaque
3. Other Information – PAC Info
Below shows the EAP-FAST process diagram (page 155-CWSP Official Study Guide) which consist of 3 phases.
1. Phase 0 – Used for automatic PAC provisioning.
2. Phase 1 – Supplicant send outer identity. AS & Supplicant negotiate using symmetric key from PAC shared secret. Result of this phase is TLS tunnel.
3. Phase 2 – Supplicant validated within TLS tunnel. It supports several inner authentication methods, commonly use EAP-GTC when username & password used as client identity info.
 Here is a EAP-FAST authentication frame capture (Supplicant MAC 00:1b:d4:58:e6:1a)
Here is a EAP-FAST authentication frame capture (Supplicant MAC 00:1b:d4:58:e6:1a)
 EAP-FAST Phase-1 process start with Authenticator sends an “Identity Request” frame to supplicant (step 4a).
EAP-FAST Phase-1 process start with Authenticator sends an “Identity Request” frame to supplicant (step 4a).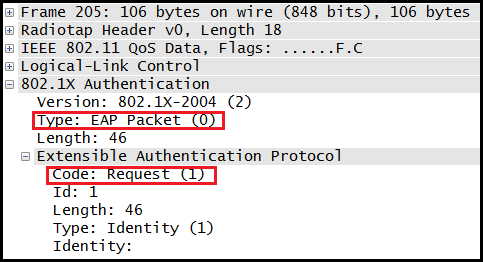 Then supplicant respond with “Identity Response” with outer identity detail in cleartext (step 4b). In here Supplicant use “anonymous” as Identity which is not real username.
Then supplicant respond with “Identity Response” with outer identity detail in cleartext (step 4b). In here Supplicant use “anonymous” as Identity which is not real username.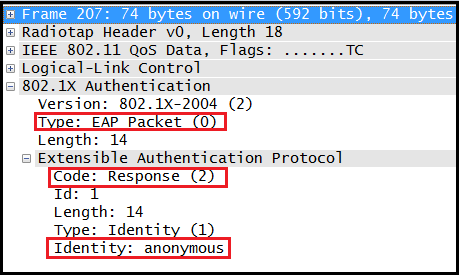 Then Authenticating Server send the EAP-FAST start message. (step 6). Note that EAP type is 43 which is EAP-FAST.
Then Authenticating Server send the EAP-FAST start message. (step 6). Note that EAP type is 43 which is EAP-FAST. Below diagram(source) shows the details packet flow of rest of phase 1 (step 7 & 8 of process diagram).
Below diagram(source) shows the details packet flow of rest of phase 1 (step 7 & 8 of process diagram).
 Then supplicant start sending client PAC (Protected Access Credential) information starting with Client Hello.
Then supplicant start sending client PAC (Protected Access Credential) information starting with Client Hello.
 Then AS will send “Server Hello” to Supplicant.
Then AS will send “Server Hello” to Supplicant.
 Then Supplicant send “Change Cipher Spec” frame to AS to complete the TLS tunnels establishment part (step 8).
Then Supplicant send “Change Cipher Spec” frame to AS to complete the TLS tunnels establishment part (step 8). That point onwards all EAP frame exchange will be TLS encrypted. Phase 2 start with Identity Request & Identity Response where real username is send inside TLS tunnel. Here are those 2 frames.
That point onwards all EAP frame exchange will be TLS encrypted. Phase 2 start with Identity Request & Identity Response where real username is send inside TLS tunnel. Here are those 2 frames.

 Then two more EAP-Request & Response frame exchange in optional PAC refresh.
Then two more EAP-Request & Response frame exchange in optional PAC refresh.

 EAP-FAST phase 2 is ends with Successful result communicate to Supplicant & Supplicant send ACK for within TLS tunnel. Here are those two frames in my capture.
EAP-FAST phase 2 is ends with Successful result communicate to Supplicant & Supplicant send ACK for within TLS tunnel. Here are those two frames in my capture.
 Once the above frame exchanged, TLS tunnel torn down & RADIUS Accept is coming from AS. Then Authenticator will pass it to Supplicant as normal EAP-Success frame (step 13)
Once the above frame exchanged, TLS tunnel torn down & RADIUS Accept is coming from AS. Then Authenticator will pass it to Supplicant as normal EAP-Success frame (step 13) Then 4-Way Handshake takes place (step 14-17).
Then 4-Way Handshake takes place (step 14-17).
Note that when using Automatic PAC provisioning, it is subject to man in the middle attack where supplicant simply trust anyone who provide PAC. If you install PAC manually on client side you can overcome this, but it becomes administrative burden.
Reference
1. EAP-FAST-7921 sample packet capture.
2. CWSP Official Study Guide – Chapter 4
Related Posts
1. CWSP- EAP Basics
2. CWSP- EAP PEAP
3. CWSP- EAP LEAP
4. CWSP- EAP TLS
5. CWSP- EAP TTLS
6. CWSP- EAP MD5

Hi Rasika,
Here is my problem ,
I am using Eap -peap ,Mschapv2 for authentication.
wireshark capture based on tcpdump shows that the server hello message (comprising of Server Hello, Certificate, Server Key Exchange, Certificate Request, Server Hello Done) is sent as 5 fragments as the length of the message is large.
The large size is mainly due to the certificate request message sent from NPS
the NPS sends 5 fragments of size 1286,1290,1290,1290,488
Howeverwpa_supplicant is able to read only 3 fragments(ignoring header) of size 1286 1290,1290 and the 4th fragment 1107 bytes
My questions are :
1.What might be the route cause for this. Checked Framed MTU value and its < 1344.
2. if we are using peap -mschapv2 ,why server is requesting for certficate .(distingueshed name length = 2048 bytes)
3. When i try with other NPS with selfsigned certs. everything is working fine eventhough server is requesting for certs.(but here distingueshed name length =0)
4. How to get distingueshed names in capture.
From the article above PAC can be pre-shared manually between supplicant and authentication server or it can be exchanged automatically.
Is Automatic option done using a different EAP-TLS session.
i.e. EAP-FAST fails initially because a PAC is exchanged and a EAP-FAST is initiated again. Is my understanding correct ?
Please share the wpa_supplicant configuration file to connect by outer method ‘EAP-MD5’