Tags
In this post we will look at WPA3-SAE Transition Mode implementation. Here is WiFi Alliance specification for WPA3-SAE Transition Mode requirement.
• When WPA2-PSK and WPA3-SAE are configured on the same BSS (mixed mode), PMF shall be set to capable (MFPC bit shall be set to 1, and MFPR bit shall be set to 0 in the RSN Capabilities field in the RSNE transmitted by the AP)
• When WPA2-PSK and WPA3-SAE are configured on the same BSS (mixed mode), the AP shall reject an association for SAE if PMF is not negotiated for that association
• A WPA3-SAE STA shall negotiate PMF when associating to an AP using WPA3-SAE Transition Mode
As you saw in my previous post when you configure an SSID with WPA3-SAE mode, only WPA3 supported client can connect to it. In the transition mode both WPA3-SAE supported client as well as WPA2-PSK supported clients can connect to same SSID. So in this mode, WPA2-PSK clients’ traffic can be decrypted where as WPA3-SAE clients’ traffic cannot be decrypted even password is compromised.
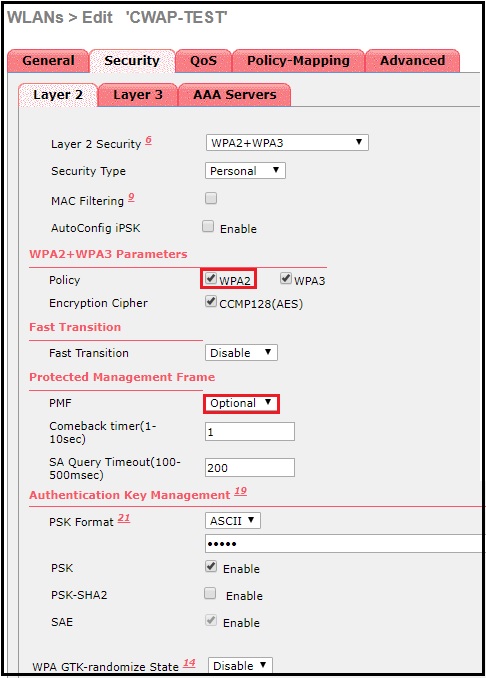
Below shows SSID security configuration that enable both WPA2 & WPA3. Note that PMF set to optional as WPA2-PSK clients may not support it.
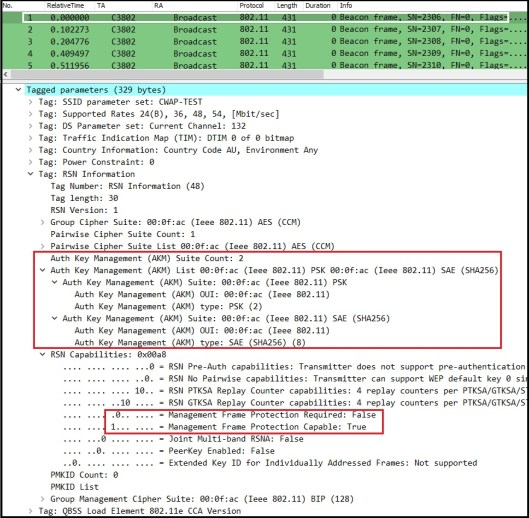
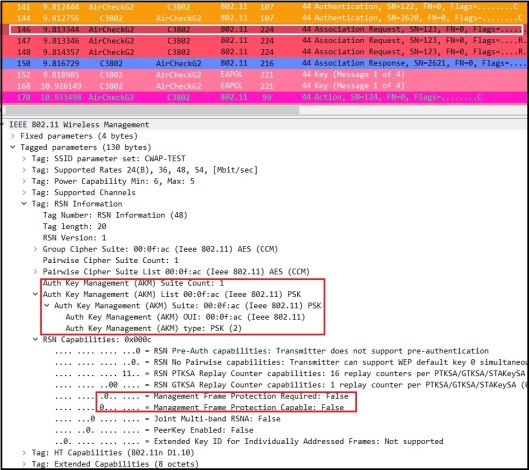
Here is a packet capture (mrncciew-wpa3-sae-transition-1.pcapng) taken using sniffer mode AP when WPA2 & WPA3 clients connecting to that SSID. If you look at a Beacon frame this time, you will see RSNE included two AKM suites (count 2).
1. 00-0F-AC:2 (PSK)
2. 00-0F-AC:8 (SAE)
Also note that AP advertise it is PMF Capable, but set PMF required to False under RSN Capabilities field.
I used google Pixel3 phone (5e:a7:ec:a8:33:ab) & NetAlly AirCheckG2 (6c:0b:84:c2:4e:99) as client devices for testing. You can filter Pixel3 Phone traffic without control frames using below Wireshark display filter.
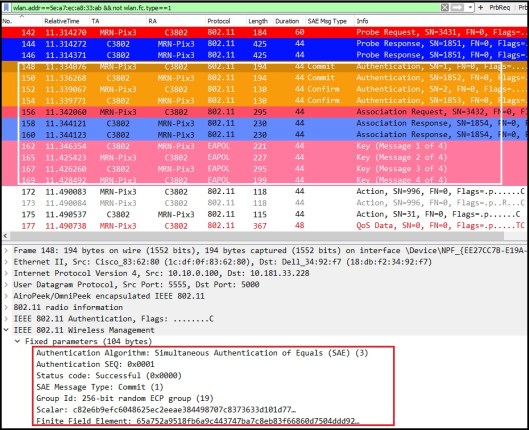
wlan.addr==5e:a7:ec:a8:33:ab && not wlan.fc.type==1
As you can see Pixel3 is go through WPA3-SAE (4 auth frames, Ass Req/Res, 4-Way handshake)
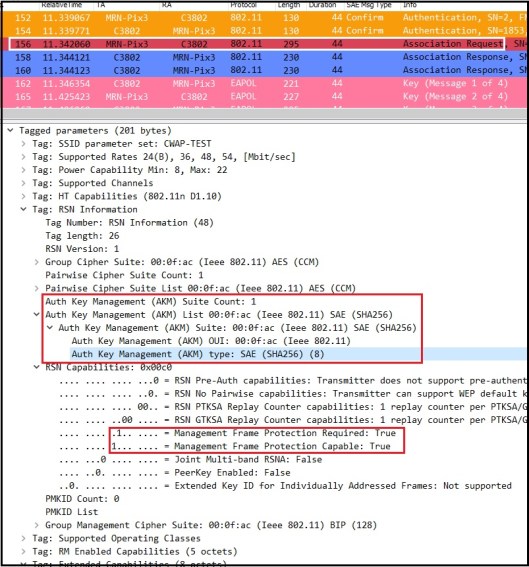
If you look at Association Request frame (#156) details, you will see AKM is SAE and both PMF Required & PMF Capable bit set to 1.
You can filter AirCheckG2 traffic without control frames using below display filter.
wlan.addr==6c:0b:84:c2:4e:99 && not wlan.fc.type==1
You will notice AirCheckG2 connecting using normal WPA2-PSK method (2 Open Auth frames, Assoc Req/Res, 4 Way Handshake). Pls note that I have used “Cisco123” as password for this SSID and you can see WPA2-PSK traffic can be decrypt easily (refer this post to know how you can do it).

Due to some reason AirCheck Traffic seems having some issue, only see TCP SYN mostly. I did same test once again and here (mrncciew-wpa3-sae-transition-2.pcapng) is the frame capture got that time. You can see AirCheckG2 is doing its testing (DHCP, DNS, ICMP) as part of connecting to given network.

If you look at Association Request frame #146 ( 147 & 148 are re-transmission of same frame #146) , you will see AKM suite is PSK and MFPC bit set to False. Since no PMF support, no group management cipher suite included in RSNE.
If you look for Robust Management Frame in this capture, you can check those frames are protected or not. There are 3 types of Management frames are considered as robust management frames when PMF in action. Those are
* Disassociation frames
* Deauthentication frames
* Robust Action Frames (action codes as per table 9-47 IEEE 802.11-2016)
0 – Spectrum Management
1 – QoS
2 – DLS
3- Block Ack
6- Fast BSS Transition (FT)
8 – SA Query
9- Protected Dual of Public Action
10 – WNM
13 – Mesh
14 – Multihop
16- DMG
18 – Fast Session Transfer
19 – Robust AV streaming
Specific to Pixel3, you will see those robust management frames are now encrypted. You can find a deauth frame (#1176 of mrncciew-wpa3-sae-transition-2.pcapng) where data get encrypted using CCMP as it is individually addressed robust management frame. Note that Protected Flag is set to 1 in that frame.

There are certain vulnerabilities of WPA3-SAE Mode. You can watch following video on those vulnerabilities. (Dragonblood A Security Analysis of WPA3’s SAE Handshake by Mathy Vanhoef). Below list is from CLUS 2019 BRKEWN-2006 presentation (see references for URL).
– Attacks on the STA
• Switch clients from WPA3 Personal to WPA2 Personal on transition mode BSS
• Downgrade Diffie Hellman Groups used in SAE
• ECC and MODP side channel timing attacks
– Attacks on the AP
• DoS from flooding spoofed authentication frames to AP
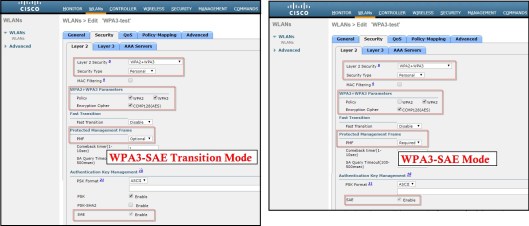
Here is a quick comparison view of AireOS WLAN security configuration for WPA3-SAE mode and WPA3-SAE Transition Mode, that we discussed in here and previous post.
We will explore WPA3-Enterprise in next Post.
References
1. BRKEWN-2006 Advancements in Wireless Security [2019 CLUS] by Stephen Orr & Bob Sayle
2. WPA3, OWE and DPP | Hemant Chaskar | WLPC Phoenix 2019
3.WPA3 support for AireOS 8.10/ IOS-XE 16.12
4. https://wificoops.com/2019/07/28/wi-fi-security-enhancements-part-1-wpa3-personal-sae/
Related Posts
1. End of Cisco AireOS?
2. Enhanced Open – Part 1
3. Enhanced Open – Part 2 (Transition Mode)
4. WPA3-SAE Mode
5. WPA3-Enterprise

This post is very useful,
Hello! I’ve been searching high and low for your WPA-3 Enterprise post but have been unable to find.. any could chance you could post the link or edit the hyperlink at the bottom of this post? The posts you’ve done on WPA-3 are the most helpful I’ve found out of any WPA-3 documentation :).
Thank you for the complement, I haven’t done that WPA3-Enterprise post yet, hope to do it within next 2-3 weeks and publish it. Will include a link to it in this post as well..
HTH
Rasika
Thank you!
I have published the blog post on “WPA3-Enterprise”, Hope you enjoy it
Rasika
Very informative article. How do we decrypt robust management frames (like action/11k etc?
how can I change that transition mode?