In this post we will see how to configure PEAP & EAP-FAST on two WLANs in a controller. ACS 5.2 is used as Authentication Server & Cisco AnyConnect used as client.
First of all you have to configure RADIUS server (ACS 5.2) to communicate with WLC & Clients. So you have to do the following.
1. Add WLC as network resource
2. Define local username/password for test user
3. Verify/Configure Policy Element for access permission
4. Apply Access Policy for network access
You can add WLC into ACS in ” Network Resources > Network Devices & AAA clients” section. You can create “Location”, “Device Type” if required in order to restrict the access based on those criteria. I have used previously created “HQ” & “WLC” location & type field in the below configuration.
Then you need to create users in ACS for this test. I have created “user1” with password “user1” for PEAP method & “user2/user2” for EAP-FAST method.You can create users in “Users & Identity Stores > Users” section. In here as well you can create Identity Groups if you want to differentiate users. I have used default “All Groups” as identity group. Since these users not accessing any network devices I have not configured enable password for them.
You have to create user2 in a similar manner. Once you create two users you can see them like this.
Next you need to verify the “Permit Access” is there under policy elements. By default there is “Permit Access” is configured on ACS5.2 unless you have configured any other custom policy elements. You can do this “Policy Elements > Authorization & Permissions > Network Access > Authorization Profiles” section as shown below. In my ACS I have already had some configurations but they are not applicable to these new users & no rules to block them.
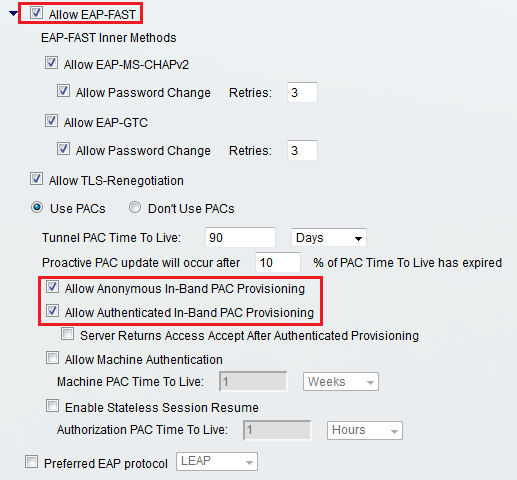
Finally you need to apply some access policy under ” Access Policies > Default Network Access” Section. First of all you need to verify EAP-FAST & PEAP is selected as allowed protocol in ACS 5.2 in this section.
Then in “Authorization” section you can configure the access policy.By selecting the Access policy & click customize button you can add filtering criteria. In my example even though I have created Location & Device type I have not used for filtering (because of this simple set up)
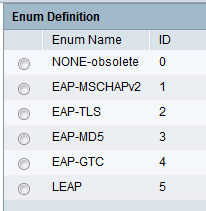
Note that I have not filtered any specific EAP types as I need to user multiple EAP types in this example. Here are the EAP Authentication options available here in ACS 5.2
Finally you need to ensure “Identity” section in Default Network Access section is configured to use “Internal Users” as we configured users locally in ACS. By click “Select” option you can choose any other available sources.(See below)
Then you need to configure WLC. First you have to add RADIUS severer to WLC & then define the two WLANs by creating the required interfaces. Below screen show how you can add RADIUS server into a WLC
In here it is not show how you can configure basic interfaces/wlans in a WLC.But show how to configure the security & advanced feature on these two WLANs.
In “data” WLAN you have to select configured RADIUS server under security tab. Other settings shows are default configurations.
Under Advanced configuration of WLAN there are few features changed from the default configuration. I have configured this based on the following cisco configuration document. I do not think those are mandatory, but just configured as guided.
PEAP and EAP-FAST with ACS 5.2 and Wireless LAN Controller Configuration Example 
You have to configure “guest” WLAN in similar fashion. But if you are familiar with WLC CLI you can configure all of these by using the following CLI configurations command. Highlighted commands are the one for changing the default settings of Advanced Tab. At least I will configure basic dynamic interfaces & wlan by using CLI to save some time. Advanced features always do via WLC GUI as it is more convenient rather remember all these CLI commands.
config interface create vlan12 12 config interface address dynamic-interface vlan12 10.10.12.10 255.255.255.0 10.10.12.1 config interface port vlan12 1 2 config interface dhcp dynamic-interface vlan12 primary 10.10.12.1 ! config interface create vlan14 14 config interface address dynamic-interface vlan14 10.10.14.10 255.255.255.0 10.10.14.1 config interface port vlan14 1 2 config interface dhcp dynamic-interface vlan14 primary 10.10.14.1 ! config wlan create 2 data data config wlan interface 2 vlan12 config wlan radius_server auth add 2 1 config wlan mfp client disable 2 config wlan security wpa enable 2 config wlan wmm allow 2 config wlan exclusionlist 2 disabled config wlan exclusionlist 2 0 config wlan broadcast-ssid enable 2 config wlan dhcp_server 2 0.0.0.0 required config wlan session-timeout 2 0 config wlan enable 2 ! config wlan create 4 guest guest config wlan interface 4 vlan14 config wlan radius_server auth add 4 1 config wlan mfp client disable 4 config wlan security wpa enable 4 config wlan wmm allow 4 config wlan exclusionlist 4 disabled config wlan exclusionlist 4 0 config wlan broadcast-ssid enable 4 config wlan dhcp_server 4 0.0.0.0 required config wlan session-timeout 4 0 config wlan enable 4
Now you are ready to test the connectivity using AnyConnect Client. In the given Cisco document they have used Microsoft client with specific profile configurations. I have used Cisco Anyconnect as it would be the client used in CCIE wireless lab exam.
Once you look at statistics section of this AnyConnect client you can verify the details.
If you select “guest” WLAN and associated it you should see something like below
Once you check the statistics you would see this client assocated with PEAPv0 which is MSCHAPv2 (PEAPv1 is GTC)
Finally you can check ACS statistics as well. Normally this would help if your client cannot associate to WLAN & if you wanted to know why is that.You can go to this report from “Monitoring & Reports > Launch Monitoring & Report Viewer > Catalog > AAA Protocol” section as shown in the below.
I have done further testing by disabling PEAPv0-MSCHAPv2 (if they stated such restrictions) forced PEAP client to used PEAPv1-GTC.
You can check this with AnyConnect & you would notice you have to select “Token” option under 802.1x to associate to the SSID.
ACS5.2 Reporting view also can be used to verify the Authentication mechanism. Notice that failure reason given PEAPv0-MSCHAPv2 is not enabled in ACS when I tried to connect PEAPv0.
Like this you have to play around with feature enable/disable & see how it really works with ACS5.2.
Related Posts
1. EAP Overview
2. AAA Basics – Part 1
3.
4.
5.
6.
7.
8.
9.









Quick question Rasika. I’m still learning ACS 5.2 myself, and was curious. In this scenario, or maybe any, I don’t see that user1 or user2 are specified to use a specific EAP method.
Is it safe to assume that user1 and user2 could use either PEAP or EAP-FAST in this situation? Since I don’t see it actually specified as to which they can actually use.
Great post!
Hi Nolan,
Yes, your assumption is correct. Both SSID allow all EAP types. Depend on client/server capability it will determine which method to use. In this example two different EAP methods use by user1 & user2 when joining the network. If needed you can join two clients devices at the sametime by using the same username but different EAP methods.
I have updated my topology diagram notes to avoid this confusion.
Rasika
Hi,
We have migrated data from ACS 4.2.1(15) to ACS 5.7. All went well except EAP-Fast authentication. I have successfully imported the master keys from old acs to new and attaching migration logs for reference. PAC is provisioned successfully for old acs 4.2 eap-fast client but inner method gets failed and we get error message saying that 2063 wrong password, though we use same username and password on any other laptop with anyconnect with eap-fast it works fine.
I did everything to troubleshoot but unable to get rid of issue. When we move old eap-fast client authentication back to old acs 4.2 then they work fine.
I checked after migration of data I had default authority ID in acs 5.7 which is something like Cisco Secure ACS and I changed it acs42 same as old acs4.2 a-ID.
It would be a great help if any one can help me to resolve this issue. I can not remove old acs from network till these old eap-fast client start working with new acs.