Management Frame Protection (MFP) provides security for the otherwise unprotected and unencrypted 802.11 management messages between APs & Clients. MFP provides both infrastructure & client support.
Infrastructure MFP
Protects management frames by adding message integrity check information element (MIC-IE) to the frames emitted by APs (and not those emitted by clients), which are then validated by other APs in the network. Infrastructure MFP is passive where it can detect and report intrusions, but has no means to stop them. Infrastructure MFP consist of 3 main components
1. Management Frame Protection
2. Management Frame Validation
3. Event Reporting
Client MFP
Client MFP encrypts management frames are sent between APs and CCXv5 clients, so that both AP & Client can take preventative action by dropping spoofed class 3 management frames (ie management frames passed between an AP and a client that is authenticated & associated). Client MFP leverages the security mechanism defined by IEEE 802.11i to protect the following types of class 3 unicast management frames
1. Disassociation frames
2. Deauthentication frames
3. QoS- WMM action
To use Client MFP, clients must support CCXv5 MFP and must negotiate WPA2 using either TKIP or AES-CCMP. To prevent attacks using broadcast frames, AP supporting CCXv5 will not emit any broadcast class 3 management frames. CCXv5 clients and APs must discard broadcast class 3 management frames.
Client MFP supplements infrastructure MFP rather replace it because infrastructure MFP continue to detect and report invalid unicast frames send to clients that are not client-MFP capable as well as invalid class 1 & 2 management frames. Infrastructure MFP applied only to management frames that are not protected by client MFP. If you require to non-CCXv5 client to associate a WLAN, client MFP should be configured as disabled or optional
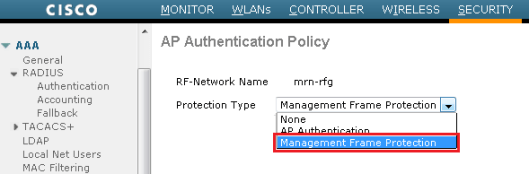
You can enable this feature globally on the controller (Security ->Wireless Protection Policies -> AP Authentication). AP Authentication & MFP is mutually exclusive features and only one can be configured on a controller. Here is the screen capture of this setting.
You can disable or re-enable infrastructure MFP per AP level as well. To do this you have to go to Advanced tab of a particular AP (Wireless -> Access Points -> All APs -<AP_Name> Advanced”) by tick or untick ” MFP Frame Validation”.
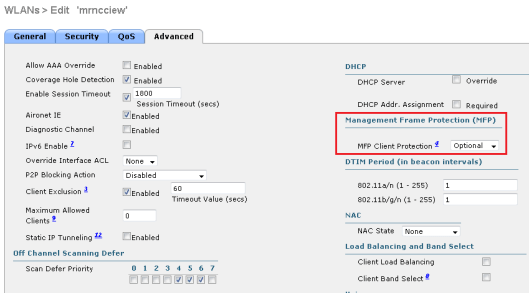
You can configure client MFP in WLAN advanced tab. By default it is set to “Optional”. If you choose this to “Required”, then clients are allowed to associate only if MFP is negotiated (ie WPA2 configured on WLC & client supports CCXv5 MFP & configured for WPA2)
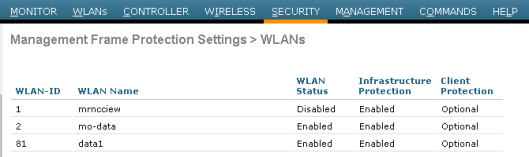
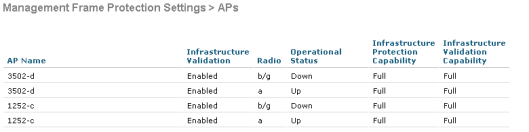
Once you configure MFP you can verify settings by using ” Security -> Wireless Protection Policies -> Management Frame Protection -> General” section.
If you are using CLI to configure this feature you can use following commands to do this.
1. To enable or disable infrastructure MFP globally for the WLC
config wps mfp infrastructure {enable|disable}
2. To enable or disable infrastructure MFP validation on an AP
config ap mfp infrastructure validation {enable|disable} Cisco_AP_Name
3. To enable or disable client MFP on a specific WLAN
config wlan mfp client {enable|disable} wlan_id [required]
You can verify MFP settings in CLI by using “show wps mfp summary” command. Here is a sample output
(4402-a) >show wps mfp summary Global Infrastructure MFP state.................. Enabled Controller Time Source Valid..................... False WLAN Infra. Client WLAN ID WLAN Name Status Protection Protection ------- ------------------------- --------- ---------- ---------- 1 mrncciew Disabled Enabled Optional 2 mo-data Enabled Enabled Optional 81 data1 Enabled Enabled Optional but inactive (WPA2 not configured) Infra. Operational --Infra. Capability-- AP Name Validation Radio State Protection Validation -------------------- ---------- ----- -------------- ---------- ---------- 3502-d Enabled b/g Down Full Full a Up Full Full 1252-c Enabled b/g Down Full Full a Up Full Full
The above is based on WLC 7.0.116.0 configuration guide.
IEEE 802.11w is the common standard for management frame protection. Windows 8 clients are support this standard & unable to connect to a network if Cisco MFP enabled unless you have compatible WLC code. Refer the below blog post from Cisco for more detail.

Hi Rasika,
I would like to inquire regarding infrastructure MFP validation on WLC code 7.6 as it is gone. Is it enabled by default already?
Please see output below from WLC:
(Cisco Controller) >show wps mfp summary
Management Frame Protection
Global Infrastructure MFP state……………. DISABLED (*all infrastructure settings are overridden)
AP Impersonation detection………………… Disabled
Controller Time Source Valid………………. True
WLAN Client
WLAN ID WLAN Name Status Protection
——- ————————- ——— ———-
6 Corporate Enabled Optional
7 Guest Enabled Optional
Based on your output above, from WLC code 7.0, infra validation is still available on the AP.
Please advise.
Thanks!
How can ap-impersonation/infrastructure be disabled per AP level? I tried looking for the option “MFP Frame Validation”. But could not find it.
Sir,
Is there any difference in PMF used in WPA3 than used in PMF?
Any new security features added to PMF in WPA3?
I mean, whether PMF is same in WPA3 and WPA2.
Hi Manesh,
There is two different things
PMF – Protected Management Frame (Cisco implementation of 802.11w)
MFP – 802.11w
In the past (with WPA2) most AP vendors support MFP, but consumer devices did not support it as WPA2 did not mandate support of MFP. Therefore difficult to enable it on your SSID as most devices does not supported it.
With WPA3, it is mandatory to support MFP and client and AP has to negotiate it.(there is no option to disable it or configure it on clients)
HTH
Rasika
thank you
Sir,
A WPA3 certified client (e.g., mobile) will support PMF, I mean, will they have option to configure MFP.?
Actually, the Wi-Fi chip used in our mobile and the mobile OS (android/ios) should both support MFP, right? Could you briefly clarify?
Thank you
From client point of view, you will not get any opiton to configure PMF. On the AP/WLC side, you have option to configure it mandatory/optional depend on how you deploy WAP3 (WPA3 only or WPA3+WPA2)
HTH
Rasika
Hi Sir,
Thank you.
So, related to answer to my last query, even if new Wi-Fi device (e.g., mobile), is WPA2 (new certifications mandates PMF) or WPA3 certified, users need not to configure anything on clients. Such clients can connect to router, if it supports or mandates PMF. Such clients can also connect to router if it does not support PMF.
Is mu understanding correct?