EAP-PEAP (Protected Extensible Authentication Protocol), creates an encrypted TLS tunnel withing which the supplicant’s inner identity is validated. Sometime it is referred as EAP within EAP. There are 3 major versions of PEAP.
1. EAP-PEAPv0(EAP-MSCHAPv2)
2. EAP-PEAPv0(EAP-TLS)
3. EAP-PEAPv1(EAP-GTC)
PEAPv0 & PEAPv1 both refer to the outer authentication method and are the mechanism that create the secure TLS tunnel to protect subsequent authentication transaction. The EAP protocol enclosed within parenthesis (ie MSCHAPv2, TLS & GTC) is the inner EAP protocol.
Below shows the EAP-MSCHAPv2 process.
 PEAP Phase1
PEAP Phase1
1. Authenticator sends an EAP frame requesting identity of the supplicant.
2. Supplicant responds with EAP Response frame with clear text outer identity(not the real username)
3. Authenticator forwards outer identity response to Authenticating Server.
4. AS sends the server certificate down to the supplicant & Supplicant validate server-side certificate.
5. An encrypted point-to-point TLS tunnel is created between Supplicant & AS.
PEAP Phase2
1. AS requests the real identity of the supplicant.
2. The supplicant respond with the inner identity, which is real username.
3. AS sends an EAP request with challenge
4. Supplicant sends an EAP response with hashed challenge response.
5. AS send an EAP request with EAP-MSCHAPv2 success.
6. Supplicant sends an EAP response with ACK.
Once Phase 2 completed, TLS tunnel will be torn down & AS send RADIUS Acceess Accept msg where Authenticator send it to Supplicant as “EAP-Success” (or EAP-Failure). Then 4-Way Handshake EAPOL-Key exhange (M1-M4) occures.
 Here is the Identity Request frame (step 4a)
Here is the Identity Request frame (step 4a)
 Here is the Identity Response frame (step 4b). This is sending the outer Identity & may not be the real username (in my case Supplicant – 7921 phone use the real username)
Here is the Identity Response frame (step 4b). This is sending the outer Identity & may not be the real username (in my case Supplicant – 7921 phone use the real username)
 Here is the Start-PEAP (an EAP Reuest type) message (step 6).
Here is the Start-PEAP (an EAP Reuest type) message (step 6).
 Server certificate validation (step 7) include multiple frame exchange as shown in the below.(image source)
Server certificate validation (step 7) include multiple frame exchange as shown in the below.(image source)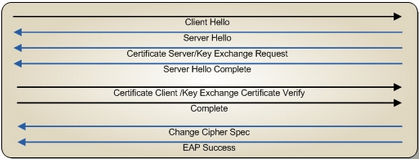 Here is the response to “PEAP-Start” frame which is “Client Hello“.
Here is the response to “PEAP-Start” frame which is “Client Hello“.
 This shows Server Hello, Certificate, Server Hello Done frames coming from AS. There may be multiple fragments as this is a large packet (due to cert size)
This shows Server Hello, Certificate, Server Hello Done frames coming from AS. There may be multiple fragments as this is a large packet (due to cert size)
 Then Client Key exchange frame goes from Supplicant to AS.
Then Client Key exchange frame goes from Supplicant to AS.
 Here is Change Cipher Spec frame.
Here is Change Cipher Spec frame.
 Here is the last frame (step 8) in Phase 1 send by the Supplicant to ensure TLS tunnel can establish since this time on.
Here is the last frame (step 8) in Phase 1 send by the Supplicant to ensure TLS tunnel can establish since this time on. Since that point onwards all packets are TLS encrypted. Here is the first frame exchange in Phase 2 which is Identify Request for real username (step 9).
Since that point onwards all packets are TLS encrypted. Here is the first frame exchange in Phase 2 which is Identify Request for real username (step 9). Here is the EAP-Response/Identity Response frame (step 10) send by the supplicant
Here is the EAP-Response/Identity Response frame (step 10) send by the supplicant Then AS will send EAP-MSCHAPv2 challenge inside the TLS tunnel to supplicant as EAP-Request frame.(step 11)
Then AS will send EAP-MSCHAPv2 challenge inside the TLS tunnel to supplicant as EAP-Request frame.(step 11)
 Here is the EAP-Response/Challenge from Supplicant (step 12)
Here is the EAP-Response/Challenge from Supplicant (step 12)
 Then AS validate client & send EAP-Request/EAP-MSCHAPv2-Success inside TLS (step 13).
Then AS validate client & send EAP-Request/EAP-MSCHAPv2-Success inside TLS (step 13).
 Then Supplicant send EAP-Response/EAP-MSCHAPv2-ACK (Step 14).
Then Supplicant send EAP-Response/EAP-MSCHAPv2-ACK (Step 14).
 So now AS sending the RADIUS accept to Authenticator & then Authenticator send that as “EAP-Success” frame to the Supplicant (step 17). This completes the Phase 2 of PEAP process.
So now AS sending the RADIUS accept to Authenticator & then Authenticator send that as “EAP-Success” frame to the Supplicant (step 17). This completes the Phase 2 of PEAP process.
 Once PEAP authentication completes, it starts EAPOL-Key exchange (4 Way handshake frame 159,161,163,165)
Once PEAP authentication completes, it starts EAPOL-Key exchange (4 Way handshake frame 159,161,163,165)
References
1. EAP-PEAP-7921 (sample packet capture)
2. CWSP Official Study Guide – Chapter 4
Related Posts
1. CWSP- EAP Basics
2. CWSP- EAP LEAP
3. CWSP- EAP FAST
4. CWSP- EAP TLS
5. CWSP- EAP TTLS
6. CWSP- EAP MD5

Hello Rasika – I was wondering if you have a post that shows 5760 and ISE configurations using 802.1x for devices that support EAP and devices that don’t support EAP. I have a situation where I have some medical devices that are using MAC addressing filtering for authenticating to the wireless network, the MACs are configured in the controller but I was wondering if I can use 802.1x for these devices as well.
Thanks;
Juan
Hi,
Am using peap Mschapv2 for authentication. But when i capture on client side, am seeing server hello ,certficate,server key exchange ,certificate request, server hello done in capture. Why AS is asking for client certs if we are using peap mchapv2? .
and the other question is if we check the certificate request packet , Not seeing any distingueshed name. (length =0 ).
How to get those distingueshed name in my capture.
AS : NPS server
client : wpa_supplcant
Hello, Thank you for posting this authentication mechanism. I just wanted to know that these packets are captured at application level or at MAC level? I needed to estimate the packet sizes for these authentication exchanges
Hi Vineet,
Packet capture over the air using wireless sniffer
HTH
Rasika
Pingback: Wireless 802.1X – Part 1 | WiFi Ty
Hi Nayarasi,
I would like to automate TLS TTLS PEAPV0 PEAPV1 PAST using wire shark .Could you please help me where can i get display filter captures
What is bogus username in step 4b??
Which step is 4b or 10 for supplicant to enter username/password to authenticate?
In phase 1, you do not want to give your real identity as anyone can see it (once they capture packets). So best practice is to use annonymous.
But most of the client devices use real identity in phase 1, so you can get the username from it.
HTH
Rasika
Hi Rasika,
thanks for you detailed info.
i have one doubt – how client is validating the server certificate? on what basis, client will get to know server sending the valid certificate?
Clients will have root certificates of the most trusted CA. The client will use that to validate server certificates
HTH
Rasika