Tags
In this post we will see how to configure WLAN on 3850 switches. In the below topology single 3850 switch stack is acting as MC/MA (WLC functionality)
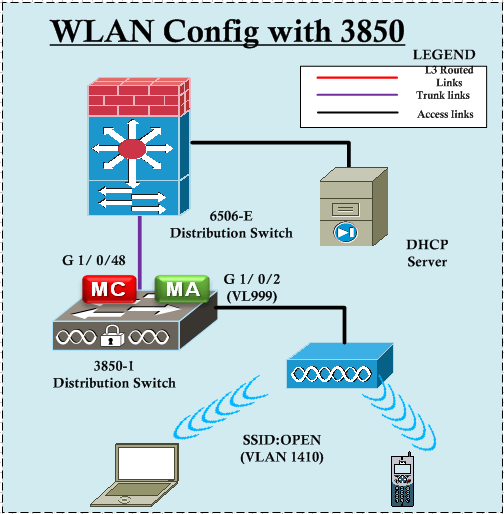 I have mainly used CLI method for the configuration & if you prefer GUI over CLI you can use that as well. Before starting WLAN configuration make sure your 3850 is configured as MC in order to act as WLC functionality. You need to have “wirelesss mobility controller” command on your switch to make it MC (by default it is MA). Also note that AP & wireless management should be on the same vlan.(999 in my case).
I have mainly used CLI method for the configuration & if you prefer GUI over CLI you can use that as well. Before starting WLAN configuration make sure your 3850 is configured as MC in order to act as WLC functionality. You need to have “wirelesss mobility controller” command on your switch to make it MC (by default it is MA). Also note that AP & wireless management should be on the same vlan.(999 in my case).
Since this 3850 act as MC (Mobility Controller), you have to define a dynamic interface where users will get map into. I have used vlan1410 (10.141.96.0/21) for this.
3850-1#sh vlan brief 999 SW-MGMT active 1410 WLN-STD-6 active 1420 WLN-STF-1 active ! interface GigabitEthernet1/0/2 switchport access vlan 999 switchport mode access spanning-tree portfast ! interface GigabitEthernet1/0/48 switchport trunk native vlan 800 switchport trunk allowed vlan 999,1410,1420 switchport mode trunk ! wireless mobility controller wireless management interface Vlan999 wireless mobility group name LTU-CA wireless rf-network LTU-CA ! interface Vlan999 ip address 10.15.4.255 255.255.254.0 ! interface Vlan1410 ip address 10.141.103.253 255.255.248.0 ! ip default-gateway 10.15.5.250
In addition to the above 6500 switch is configured as gateway for all the vlans.
interface Vlan999 description SW-MGMT ip address 10.15.5.250 255.255.254.0 ip pim sparse-mode ! interface Vlan1410 ip address 10.141.103.250 255.255.248.0 ip helper-address x.x.26.100 ip pim sparse-mode
Now we can start configuring WLAN.
3850-1(config)#wlan ?
WORD Enter Profile Name up to 32 alphanumeric characters
shutdown Enable/disable all WLANs
3850-1(config)#wlan OPEN ?
<1-64> Create WLAN Identifier
<cr>
3850-1(config)#wlan OPEN 19 ?
WORD Enter SSID (Network Name) up to 32 alphanumeric characters
<cr>
3850-1(config)#wlan OPEN 19 OPEN
Now if you look at the running configuration you will see the following
3850-1#sh run | sec wlan
wlan OPEN 19 OPEN
shutdown
It’s nothing much showing, what about all default settings of this WLAN ? If you want to see this you need to issue “sh running-config all” command. So here it is & all the default settings.
3850-1#sh running-config all | sec wlan OPEN wlan OPEN 19 OPEN accounting-list assisted-roaming dual-list assisted-roaming neighbor-list broadcast-ssid ccx aironet-iesupport channel-scan defer-priority 4 channel-scan defer-priority 5 channel-scan defer-priority 6 channel-scan defer-time 100 chd client association limit ap 0 client association limit radio 0 client association limit 0 client vlan default dtim dot11 24ghz 1 dtim dot11 5ghz 1 exclusionlist exclusionlist timeout 60 ip access-group web ip access-group ip dhcp server 0.0.0.0 ipv6 traffic-filter web none ipv6 traffic-filter none mac-filtering mfp client mfp infrastructure-protection mobility anchor sticky radio all security wpa security wpa akm dot1x security wpa wpa2 security wpa wpa2 ciphers aes security dot1x authentication-list security dot1x encryption 104 security ft over-the-ds security ft reassociation-timeout 20 security pmf association-comeback 1 security pmf saquery-retry-time 200 security static-wep-key authentication open security tkip hold-down 60 security web-auth authentication-list security web-auth parameter-map service-policy client input unknown service-policy client output unknown service-policy input unknown service-policy output unknown session-timeout 1800 wmm allowed shutdown
So by default security is set to WPA2/AES, interface map to vlan 1 (default), broadcast SSID,etc. In this first example we will change it to open authentication. Also we have mapped it to client vlan 1410 (WLN-STD-6) & remove WPA security.
3850-1(config)#wlan OPEN 19 OPEN 3850-1(config-wlan)#no security wpa 3850-1(config-wlan)#client vlan vlan1410 3850-1(config-wlan)#no shut 3850-1(config-wlan)#do sh run | sec wlan OPEN wlan OPEN 19 OPEN client vlan WLN-STD-6 no security wpa no security wpa akm dot1x no security wpa wpa2 no security wpa wpa2 ciphers aes no shutdown
Since I am using WLAN ID higher than 16, I have to use a AP Group to advertise this SSID. So I have created a AP Group called “3850” & map this WLAN onto it with interface vlan 1410. You can assign AP into AP Group by using “ap name <AP-NAME> ap-group <Group-Name>” CLI command
3850-1(config)#ap group 3850 3850-1(config-apgroup)#? default Set a command to its defaults description Specify the description for the AP group exit Exit sub-mode no Negate a command or set its defaults wlan Add WLAN to ap group 3850-1(config-apgroup)#wlan ? WORD Enter WLAN name 3850-1(config-apgroup)#wlan OPEN 3850-1(config-wlan-apgroup)#? default Set a command to its defaults exit Exit sub-mode no Negate a command or set its defaults radio-policy Configures Radio Policy on given AP-Group vlan Configures the WLANs vlan 3850-1(config-wlan-apgroup)#vlan ? WORD Specify the vlan name or vlan id 3850-1(config-wlan-apgroup)#vlan WLN-STD-6 3850-1#ap name L3502-1 ap-groupname 3850 Changing the AP's group name will cause the AP to reboot. Are you sure you want to continue? (y/n)[y]: y
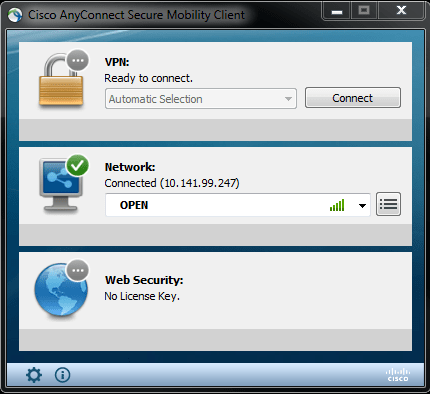
Once you do this you should be able to connect to this SSID
3850-1#show wireless client mac-address a088.b435.c2f0 detail Client MAC Address : a088.b435.c2f0 Client Username: N/A AP MAC Address : 2c3f.382b.5700 AP Name: L3502-1 AP slot : 1 Client State : Associated Wireless LAN Id : 19 Wireless LAN Name: OPEN BSSID : 2c3f.382b.570d Connected For : 95 secs Protocol : 802.11n - 5 GHz Channel : 64 Client IIF-ID : 0xc3ab4000000088 ASIC : 0 IPv4 Address : 10.141.99.247 IPv6 Address : Unknown Association Id : 2 Authentication Algorithm : Open System Status Code : 0 Session Timeout : 0 Client CCX version : 4 Client E2E version : 1 Input Policy Name : unknown Input Policy State : None Output Policy Name : unknown Output Policy State : None 802.1P Priority Tag : Not supported WMM Support : Enabled U-APSD Support : Disabled Power Save : OFF Current Rate : m15 Supported Rates : 6.0,9.0,12.0,18.0,24.0,36.0,48.0,54.0,6.0,9.0,12.0,18.0,24.0,36.0,48.0,54.0 Mobility State : Local Mobility Move Count : 0 Security Policy Completed : Yes Policy Manager State : RUN Policy Manager Rule Created : Yes NPU Fast Fast Notified : Yes Last Policy Manager State : DHCP_REQD Client Entry Create Time : 1293325 seconds Policy Type : N/A Encryption Cipher : None Management Frame Protection : No Protected Management Frame - 802.11w : No EAP Type : Not Applicable Interface : WLN-STD-6 VLAN : 1410 Quarantine VLAN : 0 Access VLAN : 1410 WFD capable : No Manged WFD capable : No Cross Connection capable : No Support Concurrent Operation : No Client Capabilities CF Pollable : Not implemented CF Poll Request : Not implemented Short Preamble : Not implemented PBCC : Not implemented Channel Agility : Not implemented Listen Interval : 90 Fast BSS Transition : Not implemented Fast BSS Transition Details : Client Statistics: Number of Bytes Received : 196611 Number of Bytes Sent : 8767 Number of Packets Received : 1477 Number of Packets Sent : 166 Number of EAP Id Request Msg Timeouts : 0 Number of EAP Request Msg Timeouts : 0 Number of EAP Key Msg Timeouts : 0 Number of Data Retries : 4 Number of RTS Retries : 0 Number of Duplicate Received Packets : 0 Number of Decrypt Failed Packets : 0 Number of Mic Failured Packets : 0 Number of Mic Missing Packets : 0 Number of Policy Errors : 0 Radio Signal Strength Indicator : -49 dBm Signal to Noise Ratio : 44 dB Assisted-Roaming Prediction List: Nearby AP Statistics: L3502-1(slot1) antenna0: 58 seconds ago -61 dBm antenna1: 58 seconds ago -51 dBm
Now if you want to configure this as WPA2/AES with PSK you can add the below configuration. Since we have disabled WPA first you need to enable it prior to configure WPA2. Also before configuring PSK you need to disable dot1x
3850-1(config-wlan)#security wpa 3850-1(config-wlan)#security wpa wpa2 ciphers aes 3850-1(config-wlan)#no security wpa akm dot1x 3850-1(config-wlan)#security wpa akm psk set-key ascii 0 Cisco123
This time you have to use the PSK defined to connect this WLAN.
3850-1#sh wireless client mac-address a088.b435.c2f0 detail Client MAC Address : a088.b435.c2f0 Client Username: N/A AP MAC Address : 2c3f.382b.5700 AP Name: L3502-1 AP slot : 1 Client State : Associated Wireless LAN Id : 19 Wireless LAN Name: OPEN BSSID : 2c3f.382b.570d Connected For : 189 secs Protocol : 802.11n - 5 GHz Channel : 64 Client IIF-ID : 0xcc9bc000000097 ASIC : 0 IPv4 Address : 10.141.99.247 IPv6 Address : Unknown Association Id : 2 Authentication Algorithm : Open System Status Code : 0 Session Timeout : 0 Client CCX version : 4 Client E2E version : 1 Input Policy Name : unknown Input Policy State : None Output Policy Name : unknown Output Policy State : None 802.1P Priority Tag : Not supported WMM Support : Enabled U-APSD Support : Disabled Power Save : OFF Current Rate : m15 Supported Rates : 6.0,9.0,12.0,18.0,24.0,36.0,48.0,54.0,6.0,9.0,12.0,18.0,24.0,36.0,48.0,54.0 Mobility State : Local Mobility Move Count : 0 Security Policy Completed : Yes Policy Manager State : RUN Policy Manager Rule Created : Yes NPU Fast Fast Notified : Yes Last Policy Manager State : DHCP_REQD Client Entry Create Time : 1296794 seconds Policy Type : WPA2 Authentication Key Management : PSK Encryption Cipher : CCMP (AES) Management Frame Protection : No Protected Management Frame - 802.11w : No EAP Type : Not Applicable Interface : WLN-STD-6 VLAN : 1410 Quarantine VLAN : 0 Access VLAN : 1410 WFD capable : No Manged WFD capable : No Cross Connection capable : No Support Concurrent Operation : No Client Capabilities
In GUI (https://10.15.4.255/wireless), you have to go to “Configuration -> Wireless -> WLAN” & then any features under General, Security, QoS, AVC & Advance tab (see below)
In next post we will see how to configure dot1x WLAN with ACS/ISE.
Related Posts
1. Getting Started with 3850
2. WLAN configs with 3850 – Part 2
3. 3850 Password Recovery
4. Converged Access Mobility
5. 3850- Flexible Netflow
6. Wireshark Capture in 3850



Thank you for your guidance on 3850 wireless configuration. You are the only one I can find in the googles that has clear directions on wlan setup with the 3850. Cisco docs all refer to the standalone WLC and the commands are not exactly the same!
Thanks for the feedback..Yes, it is very hard to find good quality cisco docs on converged access configs
Rasika
Rasika, you have done some great work on here. Many thanks.
Thank you Cumar, good these posts helps you
Rasika
I’m planning to implement something similar, but planning to add web auth on top of WPA2/pre-shared key. Do you know by any chance if 3850 supports web auth running as MC. Thanks, Krisztian
In my setup 5760 is MC & doing external Web Auth. MA tunnel guest traffic back to MC.
I think it would work even 3850 as MC, correct me if I am wrong there
HTH
Rasika
Pingback: WLC Enable on Cisco 3850 | hiteshlodhi
thanks for the posting really liked it. please let me know if I can deploy wireless topology with only 3850 on the access layer, 6500 core/dist with firewall module (collapsed core), access points and DHCP server. Its gonna be a simple deployment do you think we need any other equipment to converge it?
That will work, you need to size your (SPG-switch peer groups) carefully. Each building may be a SPG and one of the 3850 stack can be MC and all other stacks can be MAs.
Here is a useful link
http://wirelessonthego.postach.io/post/best-practices-and-golden-configs-converged-access-branch-deployment
HTH
Rasika
I am having a strange situation where I can’t see the configuration tab on the GUI. I think I have the right configuration on the 3850 but I can’t seem to be able to get it to work. Any suggestions?
What code version ?
I have version 03.06.03E
I also have AAA configured on the switch using tacacs on ISE 2.0.
I get the authentication page and I am able to access the GUI but I only get the Home, Monitor and Help tabs.
Here is the partial config:
aaa authentication login AAA group TACACS-GRUPOCESA local
aaa authentication enable default group TACACS-GRUPOCESA enable
aaa authorization config-commands
aaa authorization exec AAA group TACACS-GRUPOCESA local
aaa authorization commands 0 AAA group TACACS-GRUPOCESA local
aaa authorization commands 1 AAA group TACACS-GRUPOCESA local
aaa authorization commands 15 AAA group TACACS-GRUPOCESA local
ip http authentication aaa login-authentication AAA
ip http authentication aaa exec-authorization AAA
wireless mgmt-via-wireless
Hi Paul,
Pls check with below reference to see you have done all accordingly (Given link use ACS, but I hope ISE 2.0 is similar)
http://wirelessonthego.postach.io/post/ios-xe-5760-3850-3650-webui-privilege-level-based-access-control
HTH
Rasika
Thanks a lot. I will try it out
Hello Rasika,
Thank you for this post. It was very useful for me.
Do you know How I can create wireless network for guests witch Cisco ISE using Cisco 3850?
Any solutions?
Thank you, thank you, thank you. So much easier than the cisco docs.
Good to hear this Shawn.
Glad this post helps you in that way 🙂
Rasika
Hello Rasika,
Thank you very much for this post. I have one question though. In your setup, you use the 6500 as the gateway for wireless clients. I just wonder if the 3850 (or 3650) can act both as the MA (terminate CAPWAP tunnels) and the gateway for wireless clients at the same time?
Yes it can do that as well. In that way you need to have routing enable between MA & upstream switches.
Thank you for your quick reply. I’m planning to use 3650 switch stack at the distribution layer (with access points directly connected to them), and keep the connections between distribution and core as Layer 3 only. Therefore I need the MA to also act the gateway role for wireless clients. Just great to hear it can do that.
Hello Rasika,
Thanks for this post. I used it many times successfully. But recently I tried to configure mobility on 3650 switches. Followed your instructions step by step. In the result, SSID doesn’t show up? Any suggestions?
What is the WLAN ID number, remember you need to create AP group if WLAN_ID value > 16
HTH
Rasika
Thanks for the reply. Yes, I forgot to create AP group. Now it is Ok.
Great 🙂
good info. thank you:)
Good to hear it 🙂
I have a client indicating client state: IPLEARN on Cisco 3850 running 3.6.5 – associate with SSID but only obtains a 169.x.x.x address. Do you know of a fix/work-around?
Have you configure “ip helper address” pointing to your DHCP server on that vlan interface ?
Does your 3850 provide DHCP ? Where is that user vlan SVI defined ? on the same 3850 ?
Rasika
All vlans are defined on the 3850. It is a stand-alone unit. I did have a similar issue on another 3850 running as an MA on, but the issue didn’t present itself until we upgraded from 3.3.3 code to 3.6.4 code. The environment was one MC and two MAs; the other MA was unaffected.
I have not defined an IP helper; never been in a situation at our remote clinics where I’ve had to, unless DHCP was served up off-site.
Please with this scenario, I have connected the AP1702i on Catalyst 2960x PoE switch to power up the AP and then configure uplink on Catalyst 2960x to 3850 as trunk then 3850 (WS-C3850-24T) is configured as MC
you will not able to register that AP to your 3850. AP has to directly connect to 3850MA or MC
HTH
Rasika
HI Rasika,
thanks a lot for your post.. why many people mentioned that it is possible to connect through 2960 ? https://community.cisco.com/t5/switching/3650-amp-3850-wireless-controller/m-p/3334850/highlight/false#M405861
i really need your help. your post is the most complete steps i seen and i following the idea from your port. but my 3850 do not have poe and i dont have poe injector in hand currently.
please could you advice how can i make the AP to join the WLC at 3850?
thank you
Hi Ting,
I haven’t tested it myself. I know it is not supported by TAC or recommended.
Try your 3850 & 2960 connect via access vlan port (same as wireless management on your 3850) & see AP is able to register
HTH
Rasika
Hi Rasika,
I have a 3650 configured as an MA and a 3850 configured as a MC, both are seeing each other fine. I have an AP connected to the MA and registered there. I want to be able to centrally manage all WLANs from the MC. I don’t see that covered here, any suggestions?
rgds
Jack.
This feature not available until 16.x codes. Refer that code configuration guide for more details
http://www.cisco.com/c/en/us/td/docs/switches/lan/catalyst3850/software/release/16-3/configuration_guide/b_163_consolidated_3850_cg/b_163_consolidated_3850_cg_chapter_01010110.html#task_50C37CE3CE5C471DBB7DBE39A35ADC5B
HTH
Rasika
Thanks for the reply Rasika, I actually opened a TAC case on it as had another issue also. The TAC engineer advised me to not try and manage it Centrally but to do it separately. He advised that it was not stable enough on the current code (16.3.1) but future versions should be more stable.
Thanks for sharing this input Jack
Hi Rasika,
I have a branch with couple of cisco 3850 stacks and I need to use one of the stack as a Mobility Controller (MC) and the remaining stacks as Mobility Agents (MA) in order to deploy wireless converged access in this branch.
2 SSIDs are used on this branch to be created on the Cisco 3850 MC, one for Guest (GUEST SSID) and one for Corporate users ( Corporate SSID). each SSID is mapped to a /24 VLAN.
corporate users will be authenticated via Active Directory, as a result of Cisco 3850 MC integration with ACS that is integrated with AD.
Guest users will be authenticated via local database on the Cisco 3850 MC.
is this a working design? please support urgently.
also if 3850 is working as an MC for the whole building, will it be working as an MA at the same time for the floor it is located in?? to terminate capwap tunnels from APs in that floor.
please support.
Much appreciated.
thanks,
I hope I responded to you in CSC forum
Hi,
I have setup a 3850 at a home lab to play with the features. I have the switch connected to my ADSL modem /router as an up-link and my router is providing the DHCP.
I have created a vlan 2 for AP management on the 3850 with it’s own local DHCP.
The issue I am having is when connected to wired network off the 3850 I can SSH and access the wireless GUI no problem.
When on wireless connecting into the access points off the 3850 I can’t if even tho I get the same IP address as wired.
I think this might be some sort of protection feature to protect users on the wireless doing damage to the switch or wireless config. I know on a 5508 controller you can allow wireless to connect to GUI but I can’t find the setting on the 3850
Any ideas?
Try below command and see if that make any difference.
“wireless mgmt-via-wireless”
HTH
Rasika
Hi Rasika
I thought I tried that but you know what I didn’t! Thanks very much! been racking my head over this for a few days 🙂
Love your BLOG
Hi Rasika, i have a WS-C3850-48T that is not viewing any ap’s,
MxQoJuO02SC01Sit#sh ap sum
Number of APs: 0
Global AP User Name: Not configured
Global AP Dot1x User Name: Not configured
but i have connected an ap AIR-CAP1602I-N-K9 in the interface gi1/0/2
MxQoJuO02SC01Sit#sh cdp neigh
ap.cajero.corp
Gig 1/0/2 158 R T I AIR-SAP16 Gig 0
i follow the steps posted here carefully, the only that is different from the configurations in your notes is that my 3850 is not POE and the AP is connected with a power injector (same voltage and current that is indicated in the ap, of course, even the brand cisco), the interface has the vlan3 that i will use for wireless
MxQoJuO02SC01Sit#sh run
….
….
!
interface Vlan3
ip address 10.229.128.1 255.255.128.0
!
….
wireless mobility controller
wireless management interface Vlan3
….
….
….
MxQoJuO02SC01Sit#sh run int gi1/0/2
Building configuration…
Current configuration : 112 bytes
!
interface GigabitEthernet1/0/2
description PRUEBA DLC
switchport access vlan 3
switchport mode access
end
the only strange that i see , is that the GUI doesn’t show the system summary the information show here is only n/a
System Summary
System Time N/A
Software Version N/A
System Name N/A
System Model N/A
Up Time N/A
Wireless Management IP 10.229.128.1
802.11 a/n Network State Enabled
802.11 b/g/n Network State Enabled
Software Activation Detail
both, AP and switch can view the other via ping. and i can loggin to the WEB gui for the AP.
can you please help me with this issue…
many thanks…
greetings…
If you look at AP console output,it should give an indication what’s going on.
HTH
Rasika
did you mean that the log of the ap, will show me something about this issue..??
this is the log.
Log Buffer (1048576 bytes):
*Mar 1 00:00:15.535: %SOAP_FIPS-2-SELF_TEST_IOS_SUCCESS: IOS crypto FIPS self test passed
*Mar 1 00:00:17.299: %SOAP_FIPS-2-SELF_TEST_RAD_SUCCESS: RADIO crypto FIPS self test passed on interface Dot11Radio 0
*Mar 1 00:00:18.411: %SOAP_FIPS-2-SELF_TEST_RAD_SUCCESS: RADIO crypto FIPS self test passed on interface Dot11Radio 1
*Mar 1 00:00:19.343: not a autoconfig enabled device!!!
*Mar 1 00:00:20.455: %LINK-6-UPDOWN: Interface GigabitEthernet0, changed state to up
*Mar 1 00:00:21.511: %SYS-5-CONFIG_I: Configured from memory by console
*Mar 1 00:00:21.643: %LINEPROTO-5-UPDOWN: Line protocol on Interface GigabitEthernet0, changed state to up
*Mar 1 00:00:21.703: Starting Ethernet promiscuous mode
*Mar 1 00:00:21.707: %SYS-5-RESTART: System restarted —
Cisco IOS Software, C1600 Software (AP1G2-K9W7-M), Version 15.2(2)JB, RELEASE SOFTWARE (fc1)
Technical Support: http://www.cisco.com/techsupport
Copyright (c) 1986-2012 by Cisco Systems, Inc.
Compiled Tue 11-Dec-12 04:30 by prod_rel_team
*Mar 1 00:00:21.707: %SNMP-5-COLDSTART: SNMP agent on host ap.cajero is undergoing a cold start
*Mar 1 00:00:21.735: %SSH-5-ENABLED: SSH 1.99 has been enabled
*Mar 1 00:00:21.743: %LINK-5-CHANGED: Interface Dot11Radio0, changed state to reset
*Mar 1 00:00:21.743: %LINK-5-CHANGED: Interface Dot11Radio1, changed state to reset
*Mar 1 00:00:22.483: %LINEPROTO-5-UPDOWN: Line protocol on Interface BVI1, changed state to up
*Mar 1 00:00:22.747: %LINEPROTO-5-UPDOWN: Line protocol on Interface Dot11Radio0, changed state to down
*Mar 1 00:00:22.747: %LINEPROTO-5-UPDOWN: Line protocol on Interface Dot11Radio1, changed state to down
Dec 1 14:26:47.269: %CDP_PD-4-POWER_OK: Full power – INJECTOR_CONFIGURED_ON_SOURCE inline power source
Dec 1 14:26:48.269: %DOT11-4-NO_HT: Interface Dot11Radio0, Mcs rates disabled on vlan 0 due to not using AES encryption or encryption is not disabled
Dec 1 14:26:48.337: %LINK-6-UPDOWN: Interface Dot11Radio0, changed state to up
Dec 1 14:26:49.338: %LINEPROTO-5-UPDOWN: Line protocol on Interface Dot11Radio0, changed state to up
Dec 1 14:26:49.342: %DOT11-4-NO_SSID_OR_NO_VLAN: No SSID configured. Dot11Radio1 not started.
Dec 1 14:26:49.346: %LINK-6-UPDOWN: Interface Dot11Radio0, changed state to down
Dec 1 14:26:49.354: %LINK-5-CHANGED: Interface Dot11Radio0, changed state to reset
Dec 1 14:26:50.346: %LINEPROTO-5-UPDOWN: Line protocol on Interface Dot11Radio0, changed state to down
Dec 1 14:26:50.382: %LINK-6-UPDOWN: Interface Dot11Radio0, changed state to up
Dec 1 14:26:51.383: %LINEPROTO-5-UPDOWN: Line protocol on Interface Dot11Radio0, changed state to up
Dec 1 14:26:56.541: %DOT11-6-ASSOC: Interface Dot11Radio0, Station 400e.8503.7993 Reassociated KEY_MGMT[NONE]
Dec 1 14:27:11.569: %DOT11-6-ASSOC: Interface Dot11Radio0, Station 2827.bf85.db6f Reassociated KEY_MGMT[NONE]
Dec 1 14:29:15.254: %DOT11-6-DISASSOC: Interface Dot11Radio0, Deauthenticating Station 2827.bf85.db6f Reason: Sending station has left the BSS
Dec 1 14:29:15.262: %DOT11-6-ASSOC: Interface Dot11Radio0, Station 2827.bf85.db6f Associated KEY_MGMT[NONE]
Dec 1 14:29:41.986: %DOT11-6-ROAMED: Station 2827.bf85.db6f Roamed to 0c68.0302.3730
Dec 1 14:29:41.986: %DOT11-6-DISASSOC: Interface Dot11Radio0, Deauthenticating Station 2827.bf85.db6f Reason: Sending station has left the BSS
Dec 1 14:29:48.413: %DOT11-6-ASSOC: Interface Dot11Radio0, Station 2827.bf85.db6f Reassociated KEY_MGMT[NONE]
Dec 1 14:29:56.493: %DOT11-6-ROAMED: Station 2827.bf85.db6f Roamed to 0c68.0302.3730
Dec 1 14:29:56.493: %DOT11-6-DISASSOC: Interface Dot11Radio0, Deauthenticating Station 2827.bf85.db6f Reason: Sending station has left the BSS
Dec 1 14:30:16.452: %DOT11-6-ASSOC: Interface Dot11Radio0, Station 2827.bf85.db6f Reassociated KEY_MGMT[NONE]
Dec 1 14:30:32.268: %DOT11-6-ROAMED: Station 2827.bf85.db6f Roamed to 44ad.d956.f530
Dec 1 14:30:32.268: %DOT11-6-DISASSOC: Interface Dot11Radio0, Deauthenticating Station 2827.bf85.db6f Reason: Sending station has left the BSS
the log only shows wireless clients activity for the ssid from this ap… and the power injector conection.
Hi Rasika,
How does the software image on the AP get handled using 3850 as MC/MA? I know that using a 5508 it will push an upgrade that is appropriate version for the main image loaded on WLC. Just curious how this portion works with 3850.
Thank you in advanced.
Hi Adam,
When you upgrade 3850MA/MC switch, that package already included images for AP. So once you upgrade your switch IOS-XE image, AP will get the update from there.
HTH
Rasika
Thanks for this configuration guide! I’ve been able to get everything setup, only problem is the clients that are connecting to the AP cannot reach WAN and they can’t even be pinged from the 3850 or the AP.
I’m using an ASA 5520 for DHCP server and both the wireless and wired clients are in the same VLAN
if your SVI on ASA 5520, it may not respond to ping traffic ?
Is it possible to temporally use 3850 defined SVI for wireless & test, then you can verify wireless functionality is working.
HTH
Rasika
Thanks for the reply! It turned out to be the ip dhcp required command. As soon as I entered “no ip dhcp required” my wireless devices were able to communicate.
Page 7 of the following included that command. It made no mention of any possible issues.
Click to access b_consolidated_3850_3se_cg_chapter_010001010.pdf
Thank you for sharing that Bob. Glad to see your issue get fixed by that command
Rasika
Hi,
I have set up a 3850 controller with two APs. In our network, we prefer to use firewall as the only point of connection between the segments, so to avoid the 3850 to route between the vlans, I have not created vlan interface for the two WLANs; that is the main difference between our scenario and yours. at the moment I have difficulty with DHCP. Firewall interface is configured as relay agent but clients can`t get IP, do you have any suggestion? I could not find any cisco doc to explain how to setup WLAN with no vlan interface; not sure if it will work or there are limitations!
Many Thanks
Hi David,
I would suggest creating a vlan interface on switch for the WLAN and leave gateway as your firewall & check it.
Rasika
Hi Rasika,
many thanks for the reply.
That is fixed now without vlan interface, firewall config had issue. It was not sending the request with proper source address.
Now struggling to find a doc for cert based authentication! are you aware of any?
Maybe a stupid question, but I haven’t been able to find the answer.
Are there any functional or feature differences between a standalone Cisco 3504 and a 3650 switch with integrated MC and MA functionality?
Are all the same goodies (like clean-air spectrum analysis, etc. etc.) also supported with the 3650 switch?
Hi Peter,
It never match with AireOS features, always IOS-XE was little bit behind compare to AireOS.
Most important thing to know is Cisco has killed converged access & no longer supported beyond 16.3. x codes. So no need to worry about it anymore
Regards
Rasika
hi Nayarasi,
i found that 3850 connecting to a AP on G1/0/2 with access port vlan 999, however clients connect to SSID:OPEN with vlan 1410, how is it possible for vlan 1410 to pass through G1/0/2 to 3850?
Regards,
Ivan
Hi Ivan, AP will establish CAPWAP tunnel back to 3850, so it can carry any vlan traffic. So AP connected switchport configure as simple access vlan, however SSID can configure for any other vlan.
HTH
Rasika
what type of access point model can join 3850 MC i have 1800 AP that is not joining only 1600 are joining