Tags
In this post we will see how QoS mapping works in Converged Access switch platform (3850/3650). I have used IOS-XE 3.3.01SE image for this post (It is important since behaviour is keep evolving this CA software product suit)
Switch Ports Model SW Version SW Image Mode
------ ----- ----- ---------- ---------- ----
* 1 56 WS-C3850-48P 03.03.01SE cat3k_caa-universalk9 INSTALL
To test this out we will use the below topology where 3850-1 switch stack acting as MC/MA (WLC integrated switch).
 Here is the basic config of 3850-1 where it act as MC/MA
Here is the basic config of 3850-1 where it act as MC/MA
vlan 1410 name WLN-STD-6 ! vlan 1610 name NET-WAP-1 ! interface Vlan1410 ip address 10.141.103.241 255.255.248.0 ! interface Vlan1610 ip address 10.161.33.21 255.255.254.0 ! wireless mobility controller wireless management interface Vlan1610 ! interface GigabitEthernet1/0/2 description L1142-1 switchport access vlan 1610 switchport mode access spanning-tree portfast ! interface GigabitEthernet1/0/11 description VOIP-1 switchport access vlan 13 switchport mode access switchport voice vlan 989 spanning-tree portfast ! wlan 3850 17 3850 no broadcast-ssid client vlan WLN-STD-6 radio dot11a no security wpa no shutdown ! ap group 3850 wlan 3850 vlan WLN-STD-6
Here is a wireless sniff capturing Signaling & RTP media traffic coming from the 7925G. As expected, Signalling traffic having CS3 as DSCP with priority 4 as WMM-UP (or 802.11e) & RTP media traffic having EF as DSCP with priorty 6 as UP.
 Now lets see a packet capture at G1/0/2 (wireless port connected to L1142-1). Here is a RTP packet coming from the phone. As you can see AP is encapsulated the original packet into CAPWAP with src as AP IP & dst as 3850 wireless mgt IP. Interestingly outer DSCP is set to default (0x00). Even signalling packet outer DSCP set to default (capture not shown here).
Now lets see a packet capture at G1/0/2 (wireless port connected to L1142-1). Here is a RTP packet coming from the phone. As you can see AP is encapsulated the original packet into CAPWAP with src as AP IP & dst as 3850 wireless mgt IP. Interestingly outer DSCP is set to default (0x00). Even signalling packet outer DSCP set to default (capture not shown here).
 Why these set to Default ? If you remember the QoS Touch point post when traffic goes to wireless to wired, default behavior is UNTRUST. So you have to remove that from your switch config as shown below.
Why these set to Default ? If you remember the QoS Touch point post when traffic goes to wireless to wired, default behavior is UNTRUST. So you have to remove that from your switch config as shown below.
3850-1#sh run | in qos qos wireless-default-untrust 3850-1#conf t Enter configuration commands, one per line. End with CNTL/Z. 3850-1(config)#no qos wireless-default-untrust
Once you remove this default behavior you can see the outer CAPWAP is same as the original packet DSCP.(in RTP packet it is EF). Here is the packet capture this time on G1/0/2.
 Now let’s get a capture at G1/0/11 where VoIP phone is connected to see what QoS values go there. You can see that outer CAPWAP DSCP equivalent CoS (ie 5) in the 802.1q header (as phone switch port configured for both voice & data vlan)
Now let’s get a capture at G1/0/11 where VoIP phone is connected to see what QoS values go there. You can see that outer CAPWAP DSCP equivalent CoS (ie 5) in the 802.1q header (as phone switch port configured for both voice & data vlan)
 Below diagram summarize these QoS mapping changes when traffic going from a wireless port to wired port. When wireless frame gets into AP, it will map original IP packet DSCP value onto CAPWAP outer DSCP as shown below.This outer CAPWAP DSCP value get translated to inner packet DSCP if traffic going out via access port (or CoS if it is going out of a trunk port)
Below diagram summarize these QoS mapping changes when traffic going from a wireless port to wired port. When wireless frame gets into AP, it will map original IP packet DSCP value onto CAPWAP outer DSCP as shown below.This outer CAPWAP DSCP value get translated to inner packet DSCP if traffic going out via access port (or CoS if it is going out of a trunk port)
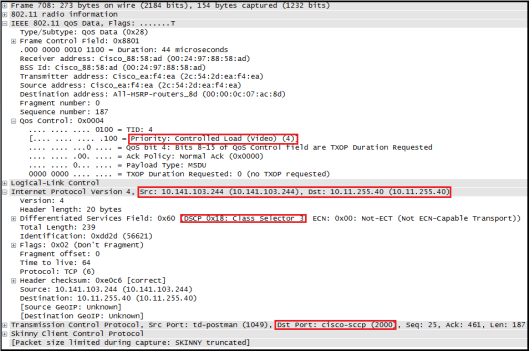
 On the reverse direction (Wired Phone to wireless phone) you can see the QoS preserved as long as you removed this default UNTRUST behavior between Wireless & Wied. (Between Wired to Wired it is TRUSTED by default). Here is the VoIP-1 to 7925G RTP traffic at G1/0/11 (Wired Port)
On the reverse direction (Wired Phone to wireless phone) you can see the QoS preserved as long as you removed this default UNTRUST behavior between Wireless & Wied. (Between Wired to Wired it is TRUSTED by default). Here is the VoIP-1 to 7925G RTP traffic at G1/0/11 (Wired Port)
 Here is the capture at G1/0/2 (Wireless port)
Here is the capture at G1/0/2 (Wireless port)
 Here is the downstream wireless traffic to 7925G. You can see outer CAPWAP DSCP is mapped to WMM_UP value (Priority 6).
Here is the downstream wireless traffic to 7925G. You can see outer CAPWAP DSCP is mapped to WMM_UP value (Priority 6).
 Below diagram summarize these QoS mapping when traffic going from a wired port to a wireless port.
Below diagram summarize these QoS mapping when traffic going from a wired port to a wireless port. Reference
Reference
1. BRKCRS-2890 – Converged Access Quality of Service
Related Posts
1. 3850 QoS – Part 1 (QoS Touch Points)
2. 3850 QoS – Part 2 (Queuing Models)
3. 3850 QoS – Part 3 (Port specific QoS Roles)
4. 3850 QoS – Part 5 (Traffic Classification)

Pingback: 3850 QoS – Part 3 (Port Specific QoS Role) | ytd2525
Pingback: Cisco iOS | KB